I really can’t say about the u1 open source hardware there. I would be leery of "WE HAVE UPDATED THE BIOS AND THERE IS NO LONGER A BIOS PASSWORD -
BIOS IS FREE AND CLEAR TO MAKE CHANGES" It may be fine but it would worry me that it was hacked and you can no longer update the bios now or if you update the bios it would be password locked again.
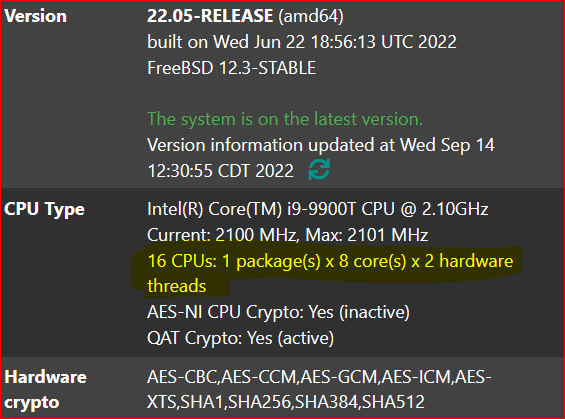
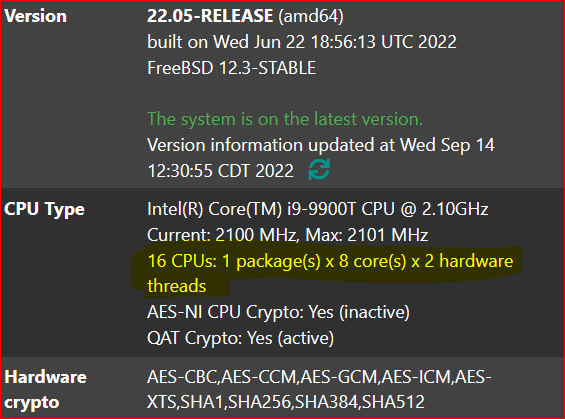
The main thing about pfSense with the cpu is you want cores/threads, which pfSense see’s as cpus. Speed/Ghz isn’t as important as the number of cores/threads. Don’t forget about energy consumption. My pfSense router, modem and switches use 65w of power.
An old dell desktop with a 4 port intel nic would work just as well and be cheaper, imo. 1u chassis is going to be loud. Those small fans will make a lot of noise. I have 5 fans, 2 14" intake fan, 2 cpu tower cooler 12" fans, 1 12" exhaust fan in a mini atx case which stays at 37’C at idle and 41’C maxed out that has no fan noise.
I would recommend getting something cheap to start with, get your feet wet with pfSense and then decide what you really want.
You can take a desktop case and place it at the bottom of your rack or get a rack shelf for it. Don’t limit yourself on a 1u server.
I didn’t dig to hard but for example, something like this: Dell Precision Tower 7810 Workstation | Tech Supply Direct
https://www.techsupplydirect.com/dell-x520-da2-10gbe-dual-port-pci-e-converged-network-adapter-card/
632.00 +85.00 + discount 10%? use code (LTSERVICES) + free shipping
gets you 8 core processor or better if you want to spend more, ecc ddr4 ram, video card to add a monitor if you want (so you can work directly from the console with a keyboard, instead of ssh), and a 10gig spf+ 2 port adapter (To use dac cable to the switch, which has lower latency and heat generation than a rj45 plug). With a fiber connection you might be able plug the fiber line directly to the pfSense router instead of using the company’s converter (there are youtube videos about this). This would give you expansion slots to add more network ports or a QAT card if so desired in the future.
1x Intel Xeon E5-2630 v3 2.4GHz (3.2GHz Turbo) 8 Core Processor - 20MB Cache - 85W - (DDR4-2133MHz) [Add $32.00]
16GB (2x 8GB) DDR4-2133 PC4-17000R ECC Registered Dual In-line Memory Modules [Add $80.00]
1x Nvidia NVS310 512MB GDDR3 64-bit - 2x DP 1.2 (Entry-Level 2D) Graphics Adapter [Add $24.00]
10gig sfp+ adapter 85.00
There are cheaper clearance models including rack mount options
https://www.techsupplydirect.com/dell-11g-poweredge-r710-8-bay-2-5-small-form-factor-2u-server-configure-to-order/
https://www.techsupplydirect.com/hp-z620-mid-tower-workstation-configure-to-order/