pedroalvesbatista 7 minutes ago
Hi fellows !
In my research and development efforts with XCP-ng, I’m getting through a lab setup.
So, in a simpler scenario, all that I should be doing for now, is :
1. Implement rules for accessing the host and VMs from my LAN connected to my ISP modem, so I can manage everything using XOA UI;
Here, what I’m asking for some enlightment is :
What type of configuration - like pre and post routing, firewall ruleset, link agregation, default gateway etc - from the router side, should I be doing so I can access my host and VMs from my home LAN, as the router is getting internet connection in GigabitEthernet 0/0 from the ISP modem, so I’m thinking in accessing my host and VMs from my laptop.
Any tips and recommendations ?
Thanks in advance !
Reply
I am not really clear on your question, but I have a video covering how to get started with XCP-NG here
@LTS_Tom thankyou very much for your reply !
My questions is basically about configuration on my network side, as I need to access both host and VMs from my home LAN, because I have Cisco gears in place for this test lab.
I would create all the default gateways as vlan interfaces on the firewall. This will allow you to create firewall rules between all your networks. As long as you allow access between networks you should be able to reach them. You’ll also want to create trunk links from your switch to both the firewall and virtual host so that you can pass traffic across multiple VLANs.
Hi @FredFerrell thanks for replying.
Well, agree that this is a better option for easy management, but, I’m still stuck on the configuration from the router side, as none firewalling is being employed just yet.
I’m looking for setting up traffic ruleset, so I can access from my home LAN. Something more closely related to that is destination NAT. I’ve been investigating from Proxmox side, to try to learn more about accessing VMs host from outside network.
What are you using as a router? Do you have a network diagram showing how things are connected?
Right now I am assuming you have a firewall that connects to your ISP on the outside interface and then you connect to a switch on the inside interface. I would expect your XCP-ng box would be connected to the switch as well, but on a different VLAN. Let me know if this is the case.
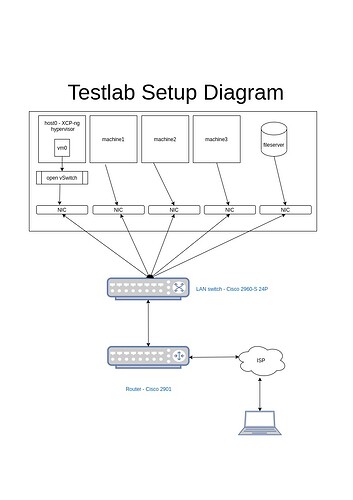
Here follows the diagram representing my setup.
Basically, the hierarchy is quite simple, my XCP-ng box is connected to switch, which is connected to router, and, that way, the router is roughly providing internet connection to my box.
I have more machines connected to the switch, but right now I’m only focusing on XCP-ng box.
And finally, I want to access my XCP-ng box from my laptop which is connected to ISP modem (let’s call it isp_lan0). This is comething like connecting from one local LAN to another “local” LAN, as they use my ISP modem as default gateway (from the router side, I configured my ISP modem IP address as being default gateway because this is needed to reach out networks outside the test lab and this is how internet connection is achieved).
Ok, so looking at your diagram it looks like you are going to assign each VM it’s own physical NIC, right? In that case you would assign the access vlan to that port it connects to on the switch.
As for the connection from the switch to the router, that should be a trunk. You’ll than create the following config on the interface for the router:
interface g0/0/0.100
encap dot1q 100
ip add 192.168.10.254 255.255.255.0
exit
Make sure to do a no shut on interface g0/0/0 if it is shutdown. That should get your intervlan routing working. You can later apply the access-lists to the sub-interfaces as needed.
As far as your laptop reaching this from the internet, I would recommend that you setup a remote access VPN. If SSL is supported I would use that, but I’m pretty sure it can run IPSec without any licensing requirements.
It’s almost quite right. All NICs referenced in this diagram points out to machine’s NICs, and the host provides connectivity through open vSwitch. But I guess I’ll really need to configure vlan routing in my switch as well in my host, and ACLs as well, so my laptop can reach the host and VMs.
IPSec and access VPN will be the next steps forward.
Thankyou very much for the help buddy, I really aprecciate it ! Have a great weekend.