Hello,
Firstly, I’ll start with saying my currently is working, but not perfectly. I don’t think my setup is all that unique so i’m reaching out, hoping someone can fix what is going wrong.
I have an inexpensive VPS I’m using just for a static ip address and to get around isp port blocking. I have Wireguard working between my VPS and PFsense at home. I’m not new to linux, but I am new to IP tables, so I followed a couple guides I found. What is happening is I have a handful of ports that I pass with NAT rules in PFsense to a mailserver (Mailcow) and http/https traffic to an Nginx instance to my webserver or mailserver. In my mailserver and I assume webserver my logs only show an ip address from the wireguard interface, not the source IP address.
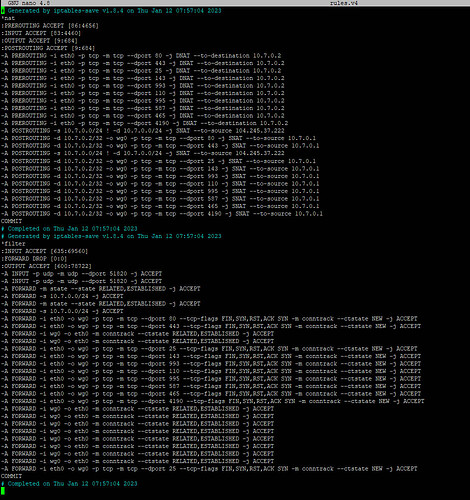
Is it possible to preserve the original ip address when I am forwarding packets through Wireguard to PFsense then to my mailserver? Have I made a mistake in my iptables or my Pfsense setup? Judging by my rules.v4 file (attached) I’m guessing I have some problems there due to the fact there are duplicate entries, but I’m not sure about the PFsense side.
For anyone who has a working setup or knowledge, I would appreciate some help.
Thanks
Sorry, only allowed to post 1 pic as a new user, so I chose the ip tables!
Are you using nginx as a reverse proxy in this setup? If that’s the case, it may be as simple as setting th X-Forward-For header (Using the Forwarded header | NGINX).
Thanks for the quick reply.
I am using a VM running ngnix for just port 80 and 443, everything else is nat rules to the mail server… That being said I believe my mail server (mailcow) does does use ngnix
Gotcha. I don’t think iptables can do this by itself. Maybe this thread could help sort it out: nginx - Iptables Port-forwarding while preserving client IP - Server Fault.
Thanks tvcvt. Not what I was hoping for, but it is what it is. If it becomes a problem, maybe I’ll upgrade and host the mail server on the VPS.
When you use SNAT, you will inevitably lose information about the original source address at the network layer. Some application layer protocols like HTTP can retain this information, but it’s not a general solution.
You would need to eliminate the SNAT in order for the servers at home to see the original source IP address. If you modify the DNAT rules to rewrite the destination to the actual IP address of the target server instead of the pfSense’s tunnel address and add a route to your home network via the pfSense’s tunnel address at the VPS, your servers at home will receive the traffic with the original source intact. However you would have to have a route on the pfSense to direct the servers’ responses back through the tunnel which could be tricky if you don’t simply change the default route.
Or just bypass pfsesne by creating a new wireguard tunnel from your mail server to your VPS.
I am interested in the same general idea but I was thinking about doing it without NAT on the VPS.