Hi
I have Wireguard setup and configured on A Windows 2019 server, I can connect from an endpoint fine to the server over the VPN.
What I can’t do is access anything other than the server that Wireguard is installed on. I added a static route in pfSense, and connecting in from a remote laptop I can ping the entire network, printers, other laptops, servers etc but I can’t access them. For example I’m trying to reach an internally hosted website on a LAN IP, which I can ping the page doesn’t display - it does on a directly connected system though. I tried accessing pfSense interface from over the VPN which also doesn’t work. Again, I get timed out. I can ping pfSense fine when connected to the VPN.
Any ideas greatly appreciated.
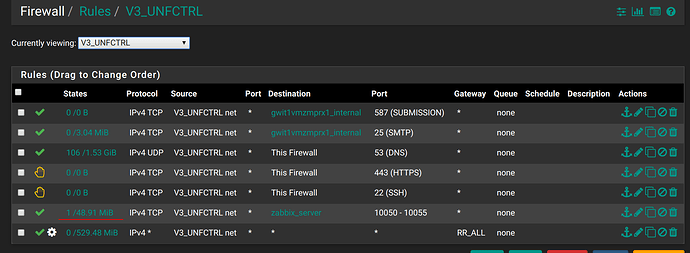
PS: for the sakes of testing, I added an allow all firewall rule in pfSense ok the LAN segment that the VPN lives in, which happens to be the same LAN the web server is on.
Thanks.
I just checked and the LAN clients can ping the Wireguard network as well as the clients connected to the VPN.
So we have flow both ways.
Anyone any ideas?
Still can’t access my network but can ping around it.
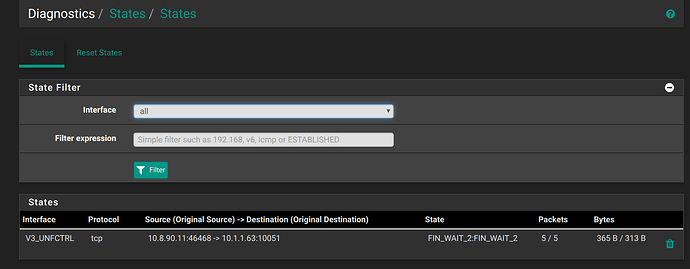
Add one specific firewall rule for one IP on the network you can’t connect to. Try to access it, ping it, etc.
Then click on the network states, and check if the state is established.
A quick update:
I replicated my Windows WG Server into a Linux one and everything worked perfect!
GET THIS!
If when I connected my VPN remotely, and connected to my pfsense here at HQ, my Server running WG would blue screen with IRQ_NOT_LESS_OR_EQUAL - How Bizzarre!!!
I have been able to replicate this also, different network, different server etc - I set a static route up in the Draytek, connected to the VPN and as soon as traffic strated flowing anywhere other than the systems that was running WG, that system then BSOD’s with same error - I wonder if there is a bug in the VPN TAP/TUN adapter in Windows.