Hi,
I have a question about VPN chaining on pfSense (v25.11.1).
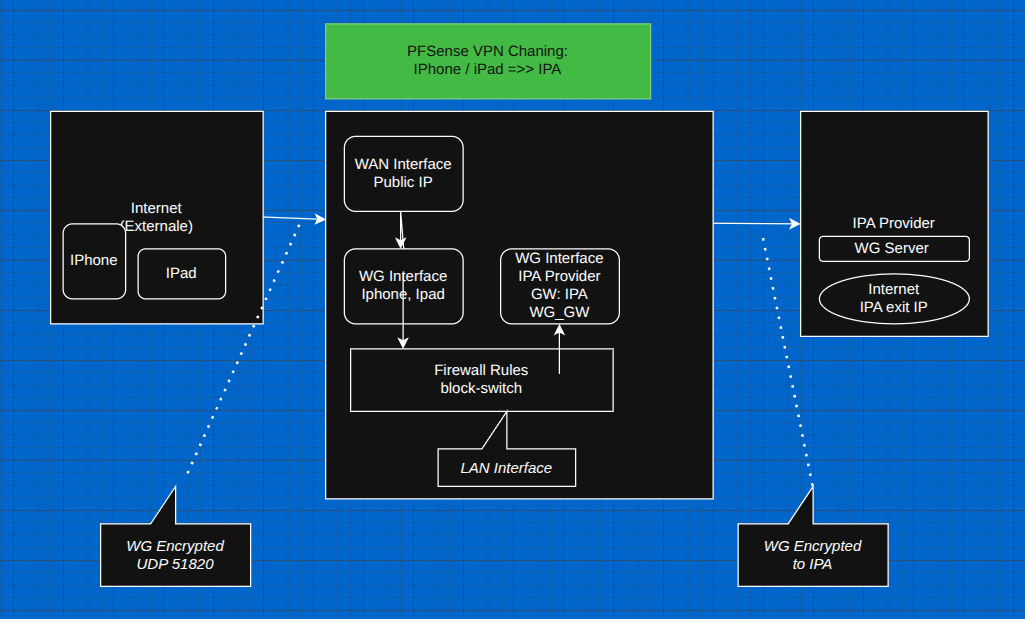
Current setup:
Both setups work correctly and I have tested the kill switch.
My question:
Is it possible to force incoming WireGuard client traffic to exit through the IPA WireGuard tunnel?
Desired flow:
Remote Client → WireGuard (pfSense server) → WireGuard (IPA client) → Internet
I assume this might be possible using interface assignments and firewall rules (policy routing).
Is this supported in pfSense, and does anyone know a guide or YouTube video explaining this setup?
Thanks!
Not sure if it’s possible since I have never had a reason to set it up. If I have an external device that I want to use a privacy VPN for I would not want to add the extra latency connecting it to my pfsense and then back out. I would simply configure that device to also use the privacy VPN.
Wouldn’t that be PIA?
Yes, exactly, it’s usually shortened to PIA.
My goal:
I plan to work around the 5-token subscription limit by routing the connections through pfSense.
I do this with OpenVPN, in your firewall rules you just need to make sure you exit via your VPN instead of the WAN.
Sometimes these paid for VPN servers can be unreliable, if you have have setup two PIA clients then you can put these into a Gateway Group. Then point your traffic to exit via the Gateway Group, if you have applied a killswitch then all traffic will stop when it goes down, however, with a GW Group the traffic will then exit via the 2nd paid for VPN client.
You ought to setup vlans, if you do, then you can get past the 5 connections limit by having the vlan exit via the paid for VPN gateway.