Tom,
In keeping with the topic in the networking / firewall forum, I would love a video sharing your thoughts on the NG firewall offerings, particularly what is good and what is smoke. Am I right that the AV / spam / phishing tools aren’t what they seem, or am I wrong? What other advanced features are actually worth the entry price? If I were considering the next step up from pfSense, what features should I be looking for? And apologies if that already exists. I’ve been soaking up so much stuff in the last few months that i haven’t made it all the way through your awesome catalog.
Thank you for all you do!
1 Like
I think the effectiveness of security services depend on the vendor. I use Gartner, Forrester, and NSS Labs to help assess the services offered by them.
I think the Palo Alto, Fortinet, and Cisco solutions are solid. Fortinet is my go to budget solution for small office, but others such as Check Point and Sophos are good too.
In my cloud hosting environment that I run on the side I use pfSense on the edge with security services running behind it.
Regarding features to look for, I would learn about the different options for high availability and advanced security. For security, I would make sure they offer DNS, URL, and file filtering, sandboxing for files, and antivirus/anti malware. If you really want to go down a rabbit hole, start looking at all the endpoint security offerings.
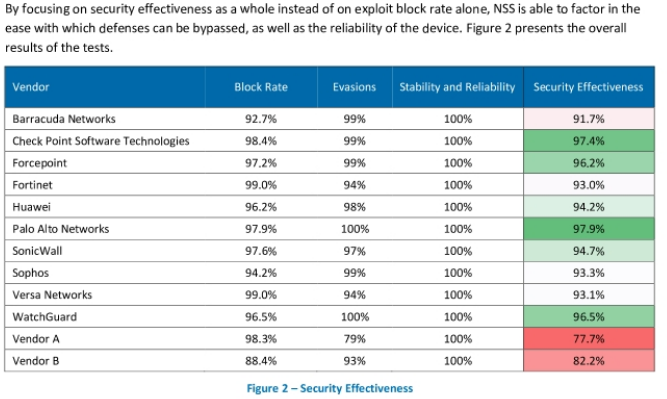
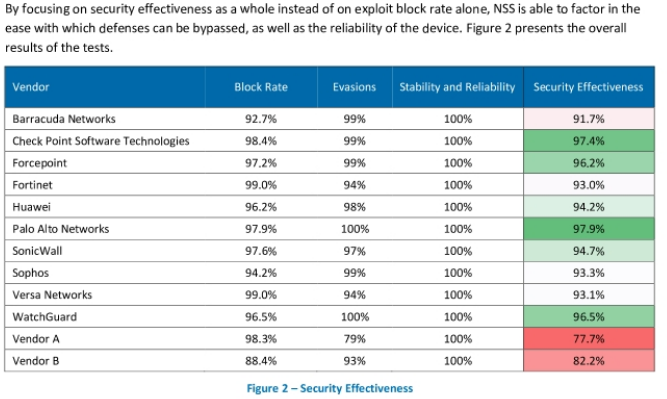
Figured I would provide a snapshot of the NSS Labs 2019 report:
My response here is not just to this post, but also your other recent post which is clearly related, and possibly the seed for this suggestion: What is your response to someone telling you "pfSense is not a NG firewall and you should be using one"? - #31 by jvedman
It is true that in many cases, inline inspection of traffic for AV, Spam, etc, targeted at HTTP, FTP, and SMTP, is getting outdated, even if used in an enterprise that does deploy a trusted root certificate to all company computers so the firewall can do MITM of the TLS traffic.
The vendors of these devices are instead putting more emphasis on their managed IP reputation lists, heuristic detection of applications based on factors that can be measured even when encrypted, and the integration of SDWAN and other buzzword features. The company I am currently at, which is just shy of being a Fortune 500 and is acting the way a proper enterprise is expected to act, is in the process of replacing an infrastructure existing of Cisco routers (non-firewall devices) and Palo Alto firewalls (operating purely as firewalls, not routers) with a “modern” NGFW/UTM product. This was chosen not just to have every router also doing firewall duties, but also because the SDWAN functionality is actually doing what was promised and allowing us to use multiple commodity connections at each location and get rid of our more expensive MPLS connections, while still maintaining good QOS for our business critical applications.
If you want to look at the feature set available with the “next step up” I can’t recommend Untangle highly enough. The home license especially is really excellent - you are getting an enterprise-grade product for consumer friendly prices. Tom has mentioned it before, that they use it for their clients that want more application usage reports and dashboards.
I’ve gone down the route of adding on tools to PFSense to do some of these advanced features, but what you are missing in that case is the integration of the features. What a properly designed NGW/UTM does is show you all together in one place everything it has learned and decided relating to a particular host, packet, or connection. What application is it? What priority for QOS does it have? If its a VOIP connection, what is the MOS score and other metrics that indicate if its a good call? What is the reputation of the server? And then for the connections it has blocked, an easy way to view the reports, and unblock false positives. When you do it piecemeal with PFSense, you have to look at each individual thing to get part of the information.
2 Likes
I have thought about doing a video on NG fiewall myths just for the clickbait type of views it would get. The whole protection offered by these companies is very oversold and the Solawinds Orion incident is proof positive of that. But web filtering is still an important aspect and so is reporting. Untangle does a good job of that for a very reasonable fee. The next video I am working on is my firewall recommendations for 2021 which is still pfsense & Untangle.
2 Likes
Thank you, Bruce. Not only for confirming some of my core beliefs, but also for giving a solid argument for a product that brings real value and not just hype. I will admit that you have me very curious about Untangle. It won’t happen soon, but I’ll definitely do a free trial at home with an eye toward the possibility of transitioning a few of our higher-end clients.
Lol. Man are you gonna hear it from the SonicWall fanboys…
And I’m here for every minute of it!
Thanks, @LTS_Tom.
In my experience none of the NGFW/UTM products out in the market that have lasted for years and gotten business recognition are just hype. The hype I believe you’re addressing is from marketing or fanboys, trumpeting that X vendor is really the best and everyone else is doing it wrong, and Y feature will save you. But in truth they all have good engineers doing good work, and usually are based on the same or similar core open source technologies.
I was really blessed in my last job to touch a wide variety of firewall vendor products. Fortinet and Sonicwall are very hard to program and require many steps to get almost anything done, but Fortinet has a really neat trick where you can partition a device and then say ports 4-6 act as a completely separate unit with nothing shared except CPU time and RAM. Watchguard’s current web interface is straightforward and makes the device a pleasure to use, it was my favorite until I learned about Untangle - but the process of doing a port forward is backwards (you’ll never figure it out without reading the documentation) and the legacy Windows program is still required for certain tasks like setting up HA. Versa is incredibly powerful, almost too powerful, they are definitely going to continue winning much more enterprise business, but their overall system won’t work for a small MSP or SMB that doesn’t have dozens of locations that need to be interconnected.
The killer feature for a lot of enterprises, honestly, is being able to do QOS based on application recognition. That used to require a completely separate “WAN Optimization” appliance. Businesses try to save money any place they can, so the internet connection is usually slower than IT would like it to be. Or the company buys cheap land for their warehouses/factories, and the only available internet connections are DSL at 6Mb down 1Mb up, and T1 lines. This is an actual condition for 25% of my employer’s branches.
Edit: By the way @jvedman the one good thing about Watchguard’s port forwarding, which is done via a firewall rule action, is that it solves your complaint about other vendors where it can be hard to get the full list of open ports and know that you’ve audited them all. There is one single firewall rule list where all rules exist, so if you don’t see a port on that list it isn’t open or forwarded. I know PFSense ends up giving you a similar effect because every port forward has an accompanying firewall rule, but other router/firewall vendors hide these automatic rules, or their underlying firewall program doesn’t require them, like iptables.
Cisco also does partitioning on their firewalls via contexting. My concern with Untangle is the lack of visibility to the effectiveness of their security services. I haven’t found any third party testing that compares to other better known brands.
The “reputable” third party testing, like NSS Labs and Gartner Magic Quadrant, operate in a “pay-to-play” fashion. Every company listed in the public report or summary had to pay to be listed there, except the top few like Cisco that everyone wants to be compared against. If you see “Vendor A” or “Vendor B” in reports like that, it means the company didn’t pay to be listed.
Compare the listed size of Untangle versus some of those other companies - Watchguard, Versa Networks - and you’ll see they are a tiny company in comparison. Frankly, they aren’t charging enough, and not doing enough marketing spin, to get big enterprises to deploy them in mass, which is how the other companies get large.
I agree with you that companies have to pay to be included, but I don’t think Untangle would have better results than those that are. The resources those companies invest in R&D are many times over what the smaller companies can make. They have a niche, but they are nowhere near the top of effective products.
IMHO, filtering at anything above or L4 on the wire is dead in the water or at the very least coming to a stop very quickly.
Everything will be encrypted so you need to monitor the traffic at a point where it’s not encrypted. That’s on the end point.
Use L3/L4 to apply QoS and hope that there are not things abusing well known ports but you can’t do much more than that.
Can’t say I agree with that. Whitelisting or filtering at L4 probably blocks more connections than it allows. This is a must for any firewall setup.
Also, we have been decrypting traffic at the network level for many years to inspect the flow for malicious content. This isn’t something that can only happen on an endpoint.
As for QoS, most SD-WAN solutions apply this based on L7 or the application. Doing it at L3 or L4 is old school.
I totally agree that whitelisting and filtering at L3/4 is very important.
I think I left an “or” in my reply that shouldn’t have been there… Not sure if that affects what I said.
My point is that newer implementations of TLS will prevent you from being able to sniff anything above L4 and will therefore make it only possible to see above L4 on device.
You can always filter traffic based on the protocol so if you can’t decrypt it you just block it.
If the protocol sticks to the correct assigned port. If it’s encrypted and on the wrong port then you have no idea what it is.
Many sites all use the same HTTPS/443 for their application data, it’s just the older systems such as VoIP that use other ports.