Hi.
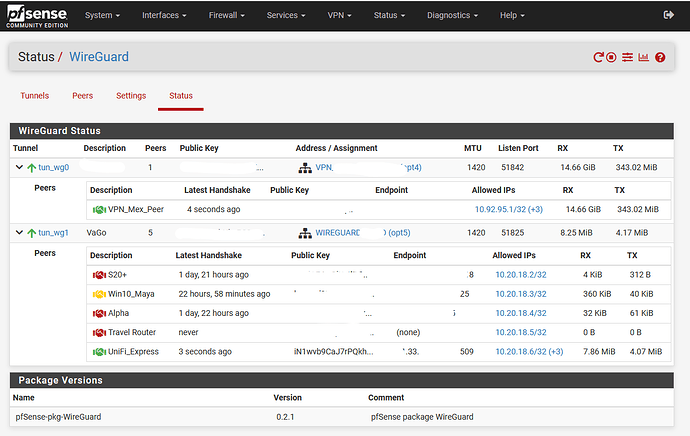
I´m trying to create a Site to Site VPN using wireguard between Unifi Express gateway and Pfsense. I already have the wireguard setup ( or that´s what i think) between the two, in the unifi I confugured as a WG client in both i can see that the connection is OK
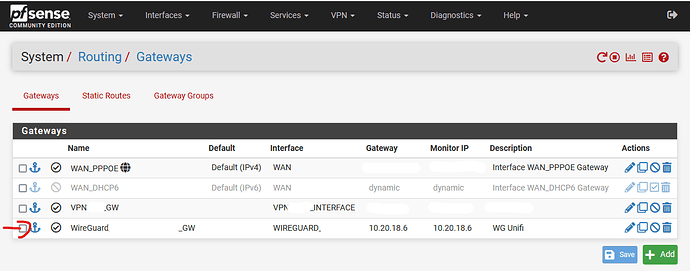
Also I configured a gateway in Pfsense and a static route redirecting the subnet that is in the side of the unifi through the WG connection.
In the unifi side I try with some firewalls configs and routing and in that side is OK, i can access the subnet of the pfsense from the unifi.
The issue is when i try to reach the subnet of the unifi from pfsense network and when i redirect all the trafic of one device from pfsense to unifi with a firewall rule. I think is something with the rules or firewall of unifi that isn´t allowing incoming traffic from the WG client, but i try with no good results (I´m quite new in the unifi ecosystem)
someone have any clue?