The last system in my network without a signed letsencrypt certficate is the unifi cloudkey controller. Excited to be this close to having them all signed.
Looking on line there are so many ways to install the certificates, yet Unifi does not seem to publish a blessed method.
The most referenced solution looks to be stevejenkins unifi_ssl_import.sh script.
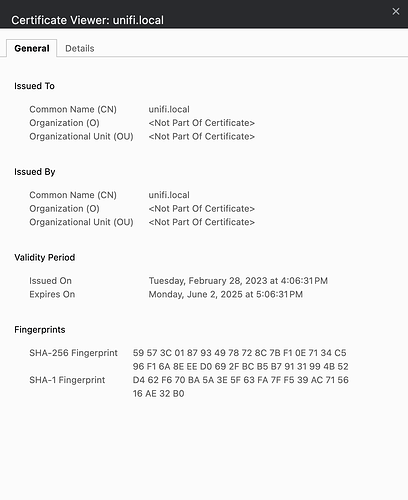
I have crafted signed certificates from letsencrypt and copied them to the unifi cloud key. Reading carefully it looks like the script inputs and directories have all be configured correctly. I have run the script with no errors. But though the script says it ran to completion surfing to the unifi’s console shows that it is still using the default unifi certificate by this image:
The cloudkey is running version 3.0.17. Has unifi changed the cert setup somehow?
Michael
Did you by chance reboot the cloud key after applying the certificates?
Yes. I rebooted the system and it still shows the old cert.
Also I copied the keystore and named it keystore.orig before I ever ran the script or made any changes. I can see by both timestamp and the diff command it is not the same as after I ran the script.
$ diff keystore.orig /usr/lib/unifi/data/keystore
Binary files keystore.orig and /usr/lib/unifi/data/keystore differ
$
Michael
Wondering if the cert needs to be made in some special way for the unifi that other devices are not as constrained by.
I used this command to issue the cert.
certbot certonly -d cloudkey.mydomain.com \
--manual --preferred-challenges dns \
--server "https://dv.acme-v02.api.pki.goog/directory" \
--config-dir=. --work-dir=. --logs-dir=.
I think this script might be what you are looking for. It looks to be pretty thorough.
Site: Glenn R.
Script: https://get.glennr.nl/unifi/extra/unifi-easy-encrypt.sh
Thanks. It also requires the ip address of the unifi cloud key to be public.
I think I am going to just live with not having a signed cert for the device. Surprised that unifi does not provide any method to do this.
Thanks again forum.
Michael
The traffic is still encrypted with the existing self signed certificate. It’s not the greatest though.
Yeah I hear you. At this point though I have the firewall configured with a lot of protection to keep people from my network. Very few folks are even on the VLAN with the Unifi so I think this falls under the “good enuf” category for now.
I am still surprised that unifi has nothing in regards to setting this up.
Off to doing other work.
Thanks to everyone and especially xMAXIMUSx.
Michael
Hey @Michael2,
Is the Cloud Key behind a pfSense firewall? You could potentially solve that problem using HA Proxy and let HA Proxy serve up the certificate instead. I would be worried the Cloud Key might not hold onto that file if it is updated even if you could install the certificate directly.
Good idea. I will check it out. Thanks!