Hello,
I have been working on getting Suricata up and running for a while and have run into some issues. I tried to install and configure it manually via CLI, but couldn’t figure out the tuning. I was able to get it to pass traffic, although it was only doing so at a rate of 1-2mbps.
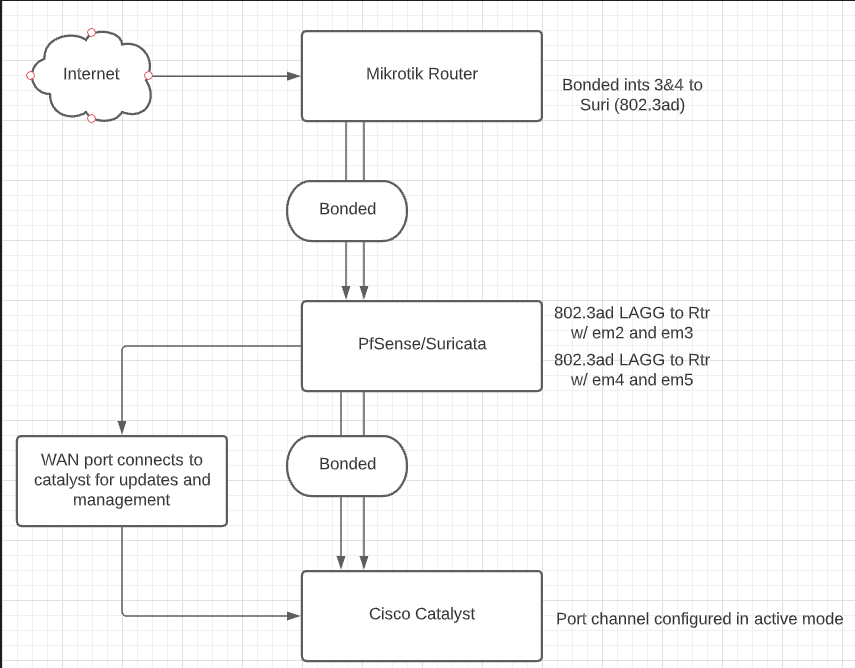
For some context, here is a quick description of my network. My internet comes into my Mikrotik router’s ethernet port. I then have two ports on the Mtik bonded and connecting to the server hosting Suricata. That server has two more bonded ports going out to my Cisco switch. All of the interfaces on all three devices show up and report no issues.
So due to the speeds I was getting and conceding the fact that I don’t understand how to tune Suricata, I looked for a more “GUI friendly” approach. I came across Lawrence Systems’ tutorials on creating a transparent bridge and IDS/IPS with pfsense.
Now I am having trouble getting this setup to pass traffic. I have two LAGGs set up in PFsense, one to the router, the other to the switch. The LAGGs are up in pfsense, the Bond shows up in the Tik, and the port channel is up on the switch (configured for active).
In my router, I can see traffic being sent into pfsense, but I do not see any traffic coming from pfsense.
From working with Suricata’s config file manually, I know that there is a copy iface parameter in its yaml configuration file that enables (what I was previously calling) bridge mode via Suricata. I am unable to find this parameter in pfsense’s GUI, nor am I sure where to the yaml in the server OS itself. From what I can tell, any changes I make will be overwritten if the server restarts which I’d prefer not to have happen.
I hope I’ve described this issue adequately, and any help/information would be greatly appreciated.
Here is a quick and dirty of how my network is setup. The LAGG interfaces in PFSense are members of the bridge that I have suricata watching. I tried doing just the LAN side, but when I didn’t get any packets set back from PFSense, I added the entire bridge to make suricata isn’t in the way (the best way I knew how at least)
One more things comes to mind, I did not test pfsense in “switch mode” without suricata running. To see if it’ll pass traffic. I figured create the LAGGs, stick them in a bridge and they should pass traffic between them. Especially since the LAGGs nor their member interfaces have IPs assigned.
Sorry for such a long post, but I wanted to give all the information I could manage to. Thanks in advance for any help or advice!