Short Version: I have Homesite and two remote locations all using OPNsense 19.1.6-amd64. All locations use PPPoE WAN, only want to enable Suricata on the home site. The remote sites connect through an OpenVPN server with xor patch, not a firewall server but on a separate VM on a VLAN. When Suricata IPS mode is enabled the remote sites seem to maintain a connection to VPN but no internet at either remote location LAN.
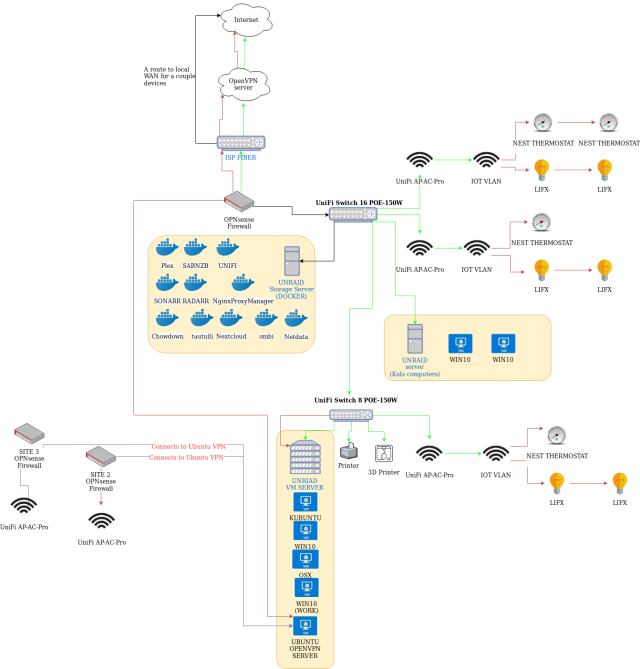
Long Version: I have three locations that are all using OPNsense 19.1.6-amd64 the Home location has the following networks.
• PPPoE WAN
• LAN
• IOT VLAN
◦ OpenVPN server with xor patch running on an Ubuntu server on IOT VLAN this how my other two sites connect.
• VPN Client
All LAN traffic with the exception of a few devices managed with aliases is routed through the VPN client. The IOT VLAN is on local ISP PPPoE WAN with the exception of the Ubuntu OpenVPN server which has a rule to use the VPN client as its gateway.
Site two and three are identical and look like this
• PPPoE WAN
• LAN
• VPN Client to site one.
Everything is working fine, but I would like to enable Suricata. Currently, I have the service enabled, but IPS mode disabled on IOT, LAN, VPN interfaces. With the following rule sets selected and set to Drop.
• ET open/botcc
• ET open/botcc.portgrouped
• ET open/ciarmy
• ET open/dshield
• ET open/emerging-attack_response
• ET open/emerging-current_events
• ET open/emerging-dos
• ET open/emerging-exploit
• ET open/emerging-malware
• ET open/emerging-mobile_malware
• ET open/emerging-trojan
• ET open/emerging-worm
When I enable IPS mode everything keeps working at the Homesite but site one and two immediately stop working unless I disconnect them from VPN. I can’t keep IPS mode enabled long enough to see what might be causing the issue as phone calls start to come in as soon as I enable it.
Figured someone here might have run into something like this or know what my issue is. Could it be the patched VPN packets tripping Suricata to drop packets? Any advice?
I have posted this on opnsense forum but not much help yet.
Also here is a diagram of my network.