3 Likes
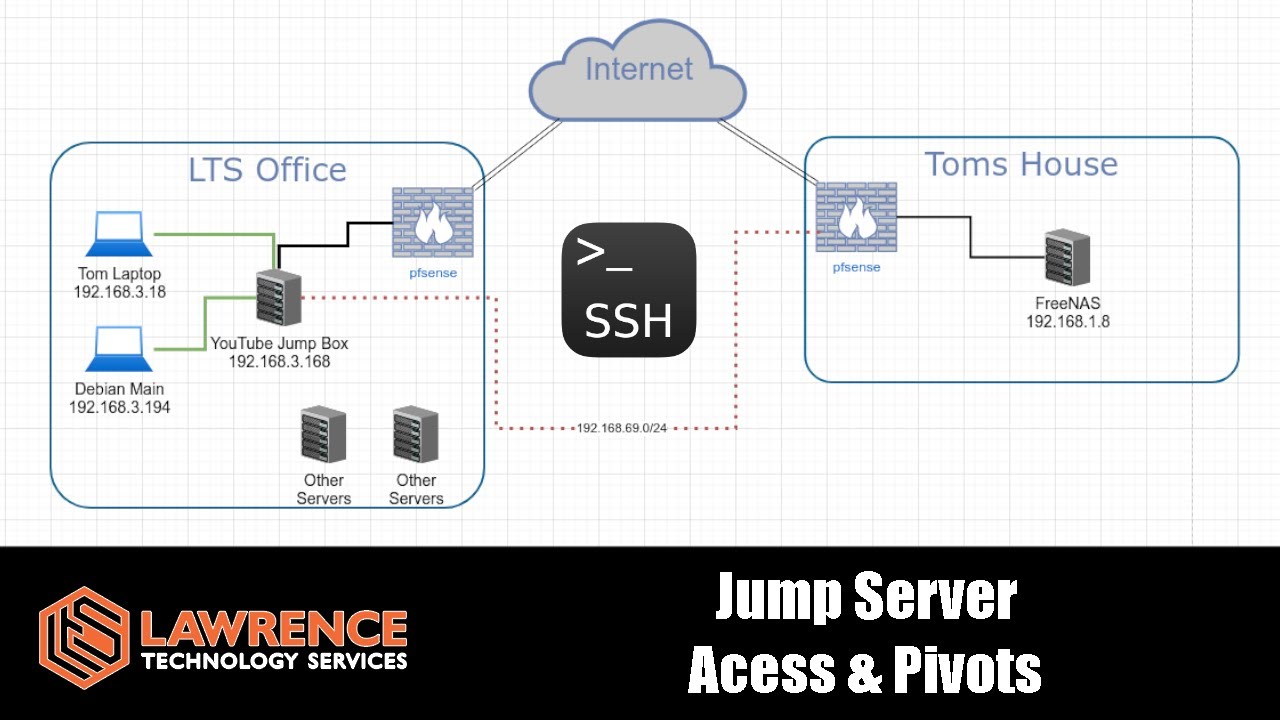
Hey @LTS_Tom,
Loved your video. You talked about how you can easily manage who has access to the jump server but what is stopping them from copying the keys once ssh’d in? Where would you store the keys securely? Of course, this is ignoring firewall rules already set in place.
Thanks
At some point you simply have to trust people. Insider threat never really goes away.