Hey!
Before you go ahead and read all of this, I just want to say that this is just idle curiosity and experimentation for learning. So basically if you find someone else who actually needs urgent help, I can wait. This is far from an ideal setup, but I’m working with what I’ve got…
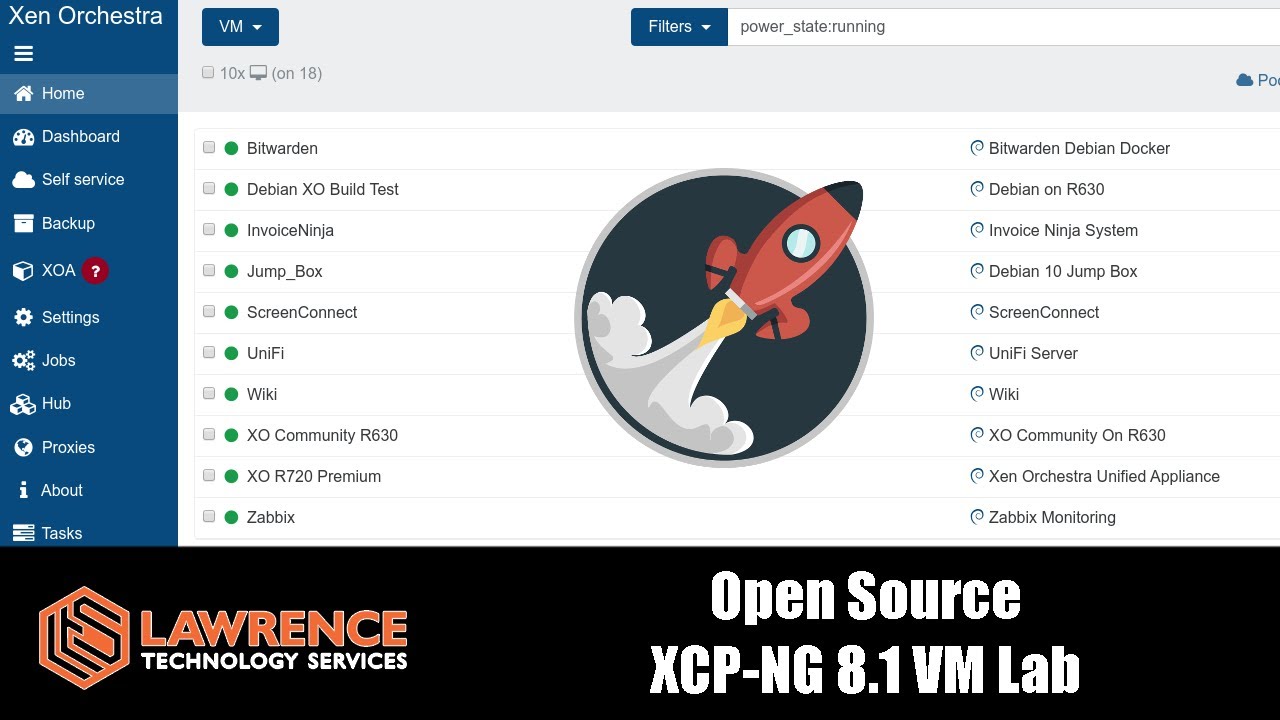
I have a XCP-NG box which is running a Nextcloud server, among other things. So far Nextcloud is working and accessible from outside my network. It’s got HTTPS and an A+ rating on nextcloud’s security check, so that’s all good, but on the internal side of my network I’m pretty ignorant about hardening and the ways forwarding ports 80 and 443 to the Nextcloud server puts the rest of the network at risk (if at all? Like I said - ignorant). For the moment I’ve un-forwarded the ports and shut down nextcloud until I understand all this.
I want to make sure that if something happens to the nextcloud server, the rest of the network is safe. My plan is to have a Pfsense VM on the same xcp-ng as nextcloud, have WAN and LAN connections through physical NICs serving the rest of the network like normal (which I have already tried, all working fine), but in addition have a separate LAN inside xcp-ng which is solely for the nextcloud (on a virtual interface (single server private network).
Basically I’m trying to achieve the same thing as a VLAN, but I don’t have a managed switch - only a big unmanaged one. I’m trying to do this with as little as hardware as possible. Just a broke student trying to get a grasp on something he finds interesting ![]()
Is it possible to have two isolated LANs on the same Pfsense? Would this actually be effective in stopping lateral network movement? If not, what should I do? Is any of this even necessary??
I’ve got a virtual xcp-ng interface showing up in Pfsense and configured as OPT1, with a static IPV4 of 192.168.10.1 and allow all firewall rules, but I can’t get internet access from a VM connected to it. I’ve googled and tried all day, but I just don’t know enough to get it working.
I’ve heard Tom talk about this kind of setup for his home network (I think?) but I can’t seem to find any more info about it, if he was using VLANs etc.
Even if I get this all working, I might have to buy another NIC anyway to make a direct connection to my FreeNAS server for VM storage. One of the two ethernet ports on my Dell PE R310 which I just bought on eBay isn’t working… The seller conveniently forgot to mention that. Still a bargin at £40 tho.
I’m just interested in how you guys would go about doing this in general terms. Once I know what I’m supposed to be doing I can learn about it and hopefully get it working.
Thanks in advance,
-Max