Hi, I have a pfSense box behind the ISP modem for quite a while, and I finally took the effort to remove the modem.
The ISP requires the device to connect on VLAN 6, IPv4 via PPPoE and IPv6 via DHCP6.
Connecting to internet went pretty well. I added a VLAN 6 on WAN interface, set the PPPoE and DHCP6 in VLAN 6, block prive networks and bogon networks just like the default WAN setting, and then boom it connected, I have internet.
But then when I tried to access my public IP as well as domain name to see if I can open my self hosted services, things go wrong and I get confused.
If I open the IP in the browser, the pfSense web GUI shows up. If I open my own domain name, then I ended up with a pfSense page warning “potential DNS rebind attack detected”. I expected to see my own website but ended up like this.
If I use a device with LTE network to open the IP and domain in the browser, it opens my website without any problem. This shows NAT is working fine.
I think because the LAN has a default rule to allow access to any network, it just access into VLAN 6 and pfSense treats it as local network.
If I added a rule to block LAN from accessing VLAN 6, then the connection to my public IP or domain name will time out.
This must be a very simple thing to solve, but I couldn’t figure it out. My question is, how should I set the rules so that I can access my own website and other services from LAN as if I’m accessing from the outside?
Sounds like you still have the web interface on port 80/443 and are port forwarding on that same port. You can change the web UI here
pfSense Configuration Recipes — Allowing Remote Access to the GUI | pfSense Documentation.
Thanks Tom for your reply. I changed the GUI port to 10443 and disabled the anti-lockout rule.
Now opening my IP via LAN will end up with time out. Opening IP:10443 will bring me to the GUI. Opening domain:10443 will end up with the “potential DNS rebind attack detected” error again.
Opening my IP via LTE on my phone will bring me to my website. Opening IP:10443 will time out which is expected.
The behavior on the phone is perfect (access from internet). But the behavior in LAN still seem like it’s in internal network because it can still reach web GUI. It feels like a routing related issue?
https://docs.netgate.com/pfsense/en/latest/services/dns/rebinding.html
That rebinding error occasionally happens when connecting via a hostname locally, which you can disable under System > Advanced > DNS Rebind Check
I’m not understanding the second part of your issue though. You don’t want to access the WebGUI on the LAN?
Yes I want to access the WebGUI.
Let me explain a bit more in detail with example:
-
I have a public IP address, something like 90.90.90.90, with a domain name mydomain.com
-
pfsense webGUI is accessible via https://10.0.0.1:10443 or https://pfsense.lan:10443
- no VLAN on the LAN interface
- VLAN 6 using PPPoE is assigned on WAN interface for internet connection
-
A few servers for NAS, website, CalDav, CardDav, each server have an IP like 10.0.0.100, 10.0.0.101 etc. They have NAT set up so I can open my website, or my phone can sync the contacts and calendars etc… NAT is set up for each port.
-
A computer or a smart phone connected in the LAN, they can open pfsense webGUI via https://10.0.0.1:10443, or via https://pfsense.lan:10443
-
The same computer or smart phone (in LAN) will open my website via https://mydomain.com, or via https://90.90.90.90
-
Anyone on the internet will open the website via https://mydomain.com, or via https://90.90.90.90
In my case, step 5 goes wrong but all other steps are totally fine. If the WebGUI is set to port 443, visiting https://90.90.90.90 will actually open webGUI instead of opening my website, visiting https://mydomain.com will end up with “DNS rebind attack”. If the WebGUI is set to port 10043, visiting either https://90.90.90.90 or https://mydomain.com will just timed out.
Basically I want any device in LAN to see my own website when I visit https://mydomain.com or 90.90.90.90, and my phone in LAN can sync the calendar via mydomain.com:8008 or 90.90.90.90:8008.
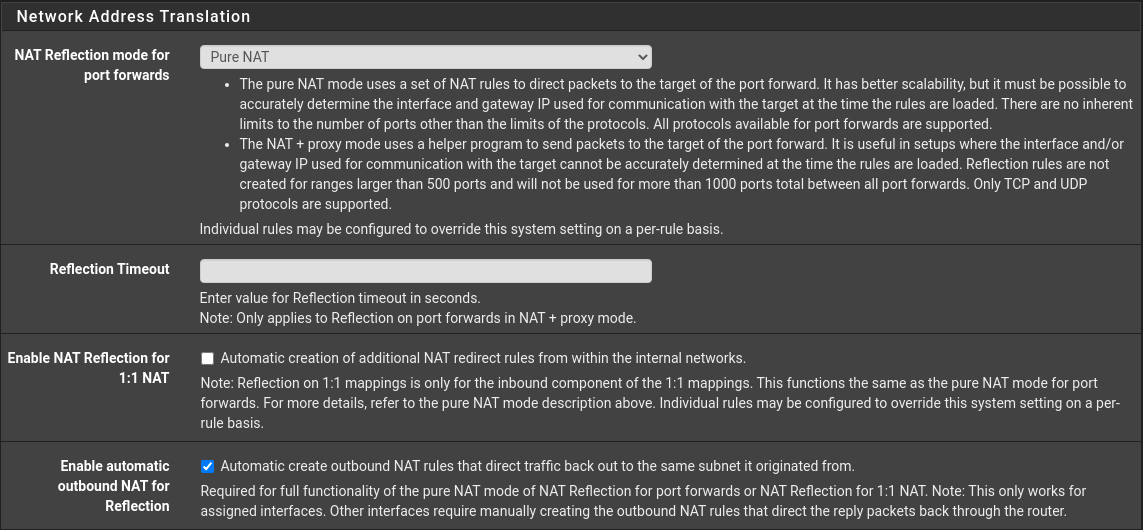
Got it. Then you want System > Advanced > Firewall & NAT > Network Address Translation and turn on Pure NAT Reflection mode for port forwards and Enable automatice outbound NAT for Reflection
Since you are accessing your own public IP from internally, you have to ensure the traffic loops back to your network as it exits your firewall. You’ll also want to follow my instructions in the link above to fix the rebind error.
Edit: If you’re doing any 1:1 NAT as well, you’ll want to enable the option for that on that page
2 Likes
Yes it works!
I was trying to find certain settings that can make the connection to mydomain.com treated as “external”. Now I understand it much better.
There is no rebind error anymore after setting the NAT correctly. I’ll leave that setting as default for now, if the rebind error occurs again I’ll change it.
Thank you Eric! I’ve learned something very useful today.
1 Like