Greetings, forum, this my first post here.
My home lab is about 2 years old now and during that time I’ve avoided playing with the router because it basically terrifies me … yawn … hence, I’ve learned almost nothing about the firewall or router config … and I’m pretty sure therein lies the solution to my DNS leaks …
But, of course, I am in this forum to hear from the experts before I waste yet another day (of my essentially worthless time) on this nonsense …
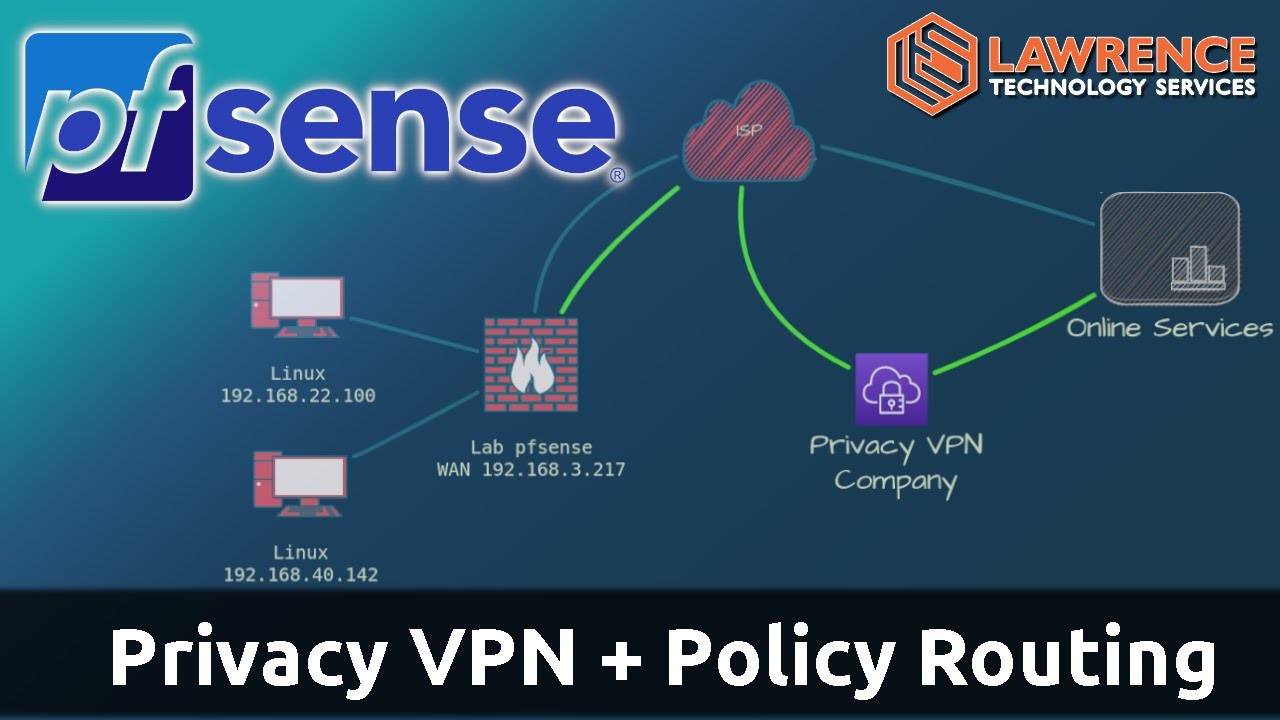
My home network has a single upstream WAN, 4 subnets on 192.168 … , three OpenVPN tunnels running on ExpressVPN which is installed on a Quotom 4125. This is gen 10 Celeron architecture, with 4 RJ45 subnet NICs …
Recently I decided to try running Pi-Hole on the home net … and so I added a spare mini to a local subnet, installed Deb 13 RC2 (req’d because the mini has Alder Lake N series integrated PCI stack) and then installed Unbound with PI-hole.
Correct operation of pi-hole/unbound with DnsSec was verified after installing those.
After setting the pi-hole IP as DNS for the test subnet and using an old laptop running Deb12 with Brave Browser, I tested for DNS leaks at dnsleaktest.com.
It failed … and everything I’ve done to try and fix it has failed as well … I was also reminded of my deep lack of understanding of how the firewall rules really work …
So, after restoring the router to its last known functional config (as of about midnight last night), I felt very happy and fortunate to have an operating home network again …
Although the Brave browser is hard coded to query upstream DNS sites (and for some reason this setting is immutable) I remain convinced the solution lies in simply configuring the firewall correctly.
I’ll leave it there as this is already way too long …
Thanks in advance for your kind attention … g