Hi all, hoping to seek some advice / understanding of setting up a mgmt vlan with the following hardware.
- pfSense on a miniPC
- L2 switch
- TP-Link AC
- TP-Link in-wall AP’s
Many thanks to the youtube video guides, I have had no issues reassigning static IP’s to Mgmt Vlan subnet for the non-pfSense devices. However, I have not been able to figure out how to set the pfSense device to the Mgmt Vlan subnet.
-
As far as I can tell the pfSense subnet is tied to LAN.
-
If I were to use LAN as the Mgmt subnet, I would need to sacrifice a dedicated port (pfSense to Switch) to avoid random access to the Mgmt subnet when plugging in new devices to untagged ports. My understanding is it would default to this as untagged network if on the trunk port.
-
I have seen some sites suggest that Advanced settings has an option to select the interface which pfSense lives on but I am unable to find this option. I am using the community edition 2.8.0
Not sure if the above understanding is accurate / makes sense. Hope to seek advice thank you!
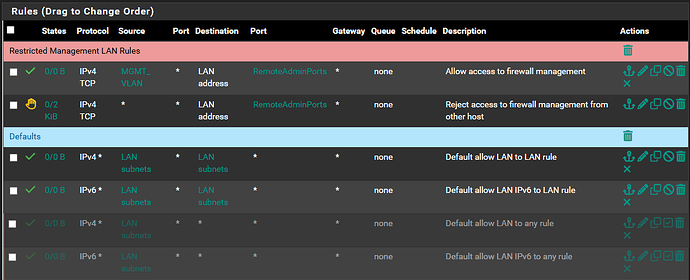
They have a guide here on restricting Web interface access which is really what you want.
Many thanks Tom for the link and the youtube vids! Have learnt alot and still learning!
I have managed to shift my Switch, AC and AP’s to the MGMT_VLAN thanks to the guide and can access webmgmt gui from a mgmt_vlan only access port on my switch.
However, I am still slightly unsure about the last rule they have shared where they pass 10.0.0.0/8 to any.
Is this a variation of the current default allow on a fresh install? Where there are 2 rules to pass IPv4 and IPv6 from LAN subnets to any?
In that case is 10.0.0.0/8 equivalent to LAN subnets in their example? Or is that some other network being referenced?
I’ve disabled the default LAN rules for future reference below, and replaced with internal only LAN to LAN rules for future-idiot-self randomly plugging into empty ports for testing.
Thank you!
Using 10.0.0.0/8 is an example of allowing rules for any networks you have that start with the 10.0.0.0. If you are using another subnet range such as 192.168.0.0/16 then you would that.
Thanks @LTS_Tom will read up more on firewall rules to be sure of what I’m doing.