I have used @neogrid’s configuration that uses the DNS forwarder to utilize the DNS servers identified in system>general. I am using Quad9 in there. The primary and secondary DNS entries both use the WAN in the clear. The NAT and Rules are all setup as recommended for my VLANs that I want traffic to go out n the clear. The I use the DNS resolver for my VLANs on AirVPN again as recommended.
When I use dnsleaktest on the VPN vlans, it is perfect. The extended tests show only AirVPN dns servers.
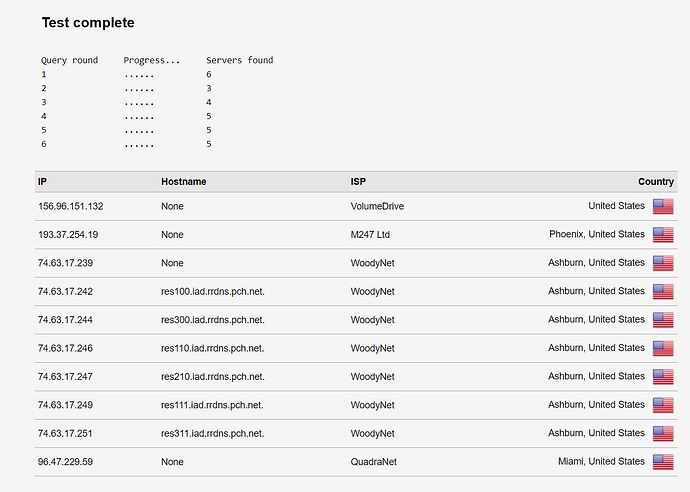
BUT, when I use dnsleaktest on the clear VLANs through the forwarder, the results are a little odd. The extended test shows my DNS traffic going out through BOTH. Some of them hit quad 9 as I would expect. But some of them hit AirVPN as if it’s going back through the resolver. This is screwing up some services that just can’t handle DNS routing through the VPN, because it keeps getting routed through the VPN for reasons unknown.
What could be causing this?
Do you have IPv6 enabled?
Nope. Not through any interface or gateway. And blocked by firewall rules.
Check the DNS servers that are found in the /etc/resolv.conf file. In my case, the system was adding the ISP’s DNS servers.
Looks like localhost, quad9 primary & secondary as I set, and whatever search local.lan means?
nameserver 127.0.0.1
nameserver 9.9.9.9
nameserver 149.112.112.112
search local.lan
local.lan is the domain assigned to your pfSense local subnet.
LOL I know. I mean IDK what it means in the context of that file, which I also know nothing about.
Ah, okay, gotcha. lol
I wasn’t sure exactly either. Let’s say I was about halfway sure. 
Apparently, if the search query (ie nslookup or dig) doesn’t contain any dots (.) in the query, the resolver will automatically add “.local.lan” to the end of the query entry.
For instance, my domain is local.pvt. If i want to look up the IP address of my media server, I can enter this…
seankane@client-mbp-sean ~ % nslookup server-media
Server: 10.80.65.254
Address: 10.80.65.254#53
Name: server-media.local.pvt
Address: 10.80.65.2
As you can see above, the query added “.local.pvt” to my query to get the result.
Does that make sense?
Sean
LOL @pedals2paddles never listen to anything I say !!!
Admittedly I only considered DNS leaks on my VPN vLAN, they looked ok. I just looked at my ISP Vlan and didn’t see any AirVPN servers.
From what you have noted down, I don’t use the localhost as a DNS, perhaps switch this off and inspect the results.
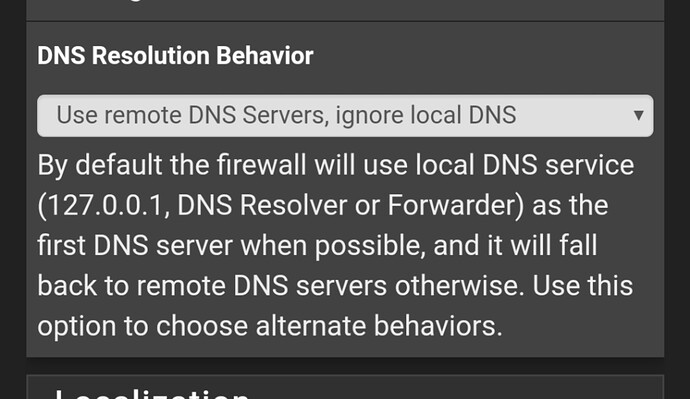
Go to System > General Setup and check “Do not use the DNS Forwarder/DNS Resolver as a DNS server for the firewall”
Mine is checked for reference, I’d like to give you the reason why but I honestly don’t recall.
If it’s not that then it may well be your DNS port forwarding having an error. As it sounds like both DNS servers are being used and the fastest result when being AirVPN gets noticed.
Haha too late. Seems thousands of people listen to what you say! Your guides were fantastic. This was the first I’ve ever set up vlans and a VPN in my life and it worked on the first try thanks to you.
And once again your suggestion did the trick. It’s a drop down selection now and I set it to only use external and problem solved.
LOL the awesome power of trial and error 
I think that localhost may work if your device only stays on one vlan and so I guess be able to resolve faster but if you swap between your ISP and VPN those DNS records must still remain on the machine.
To be honest I never noticed a slow DNS query, if it now works it should be fine.
Yes I’m on 2.4.5 I guess it has moved on 2.5