Hi, I live in Italy and the local ISP provider give to their customers their own modem/router combo. The connection also for FTTC as I’m using is provided with PPPoE method. The main problem is that I cannot put their device in bridge mode so I end up with my pfsense WAN IP as a private IP…what’s the best practice to handle this situation? I can’t get rid of their devices because it’s used for the normal telephone line circuit.
Any help?
You can put your pfsense in a DMZ on your ISP provided device. That way all traffic is passed without restriction.
Can you please explain me deeply on this? how can i do? I’ll get a public address on the wan interface in this way? 
No, you will still have your pfsense with a private adress, but everything reaching the modem public address will get to your pfsense.
its a setting in the modem config, like port forwarding, but it forwards all ports.
To setup the modem as you suggest I only have to point It to the WAN IP address I statically set on my pfsense firewall?
Can I still reach the modem with a device behind the firewall?
Yes you should be able to reach the modem. As for the setup it would be something like
Modem network
192.168.1.1
Modem DMZ
192.168.1.2
Pfsense wan
192.168.1.2
Pfsense lan
192.168.2.1
Ok thank you so much.
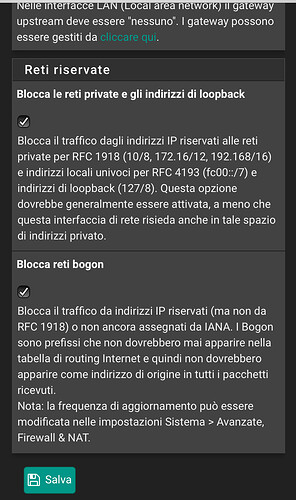
Last question… in the WAN page settings the last two option (al the bottom of the page) which creates the automatic firewall rules for the wan side, must be unchecked or can I leave them “on”?
You’ll have to uncheck both because you’ll be using a privateIP address.
Apparently everything is working fine without unchecked those…I’ll fix as you suggested but what should I expect not to work if left those checked?
In this example, does 192.168.1.2 become the gateway address for devices on the LAN?
Hi xMAXIMUSx,
I wish I knew of this group there years ago. I did the same thing with the router from my ISP so my TVs could get their program information while still running my pfSense box for my home. Great answer!
I am working on the same setup as you right now and I was also surprised that my setup works with these boxes checked. I guess people recommending to uncheck this because mostly they assume you have a testing lab and there are devices in the private WAN network which try to access the firewall and/or services of it. Then you need to uncheck both options.
Best explanation is here:
No. For LAN devices the standard gateway is 192.168.2.1 (pfsense)
So if I have the modem/router from my isp, (First NAT) then pfsense firewall box (second NAT) and my lan network and as long as I don’t have any device in the first NAT except the wan side of pfsense I can/must let those two option checked?
I would say: Correct.
My setup: Provider modem (10.0.0.138) -> pfsense WAN IP (10.0.0.1) -> LAN 10.1.0.1
On provider device I put the IP 10.0.0.1 into the DMZ. This should mean that all ports are forwarded to this IP. No device in the 10.0.0.0/range except pfsense.
Now this sentence comes into play:
They will not block port-forwarded or 1:1 traffic from an upstream router unless that device also NATs the source address to something that matches these rules.
Yes this confuses me. Because DMZ (upstream device) forwards everything to pfsense but has to NAT it somehow. Which would mean the rules should block it.
But I can reach all my Dockers and therefore I leave the two options checked until I encounter a problem with the two options. So far the majority works. Problem to solve: I can’t access the webui from the provider modem.
I think I just answered a part of my confusion. My provider modem doesn’t nat the traffic (somehow).
I logged into my company’s network and opened my home website. And in pfsense pfTop I see the public IP from my company.
what router did your isp gave you?
Hi I would like to use this system behind my Virgin Media Hub 5X ( which does not allow Modem/Mode or port forwarding) which is useless.
i have tried DMZ but I receive a DHCP address .
Any guidance would be appreciate.
No need to uncheck those boxes. The boxes only block traffic originating from private IPs. Since internet IPs do not use private IPs and are only “relayed” by the IPS router it will work fine. I used my setup like this for years!