Additional Resources:
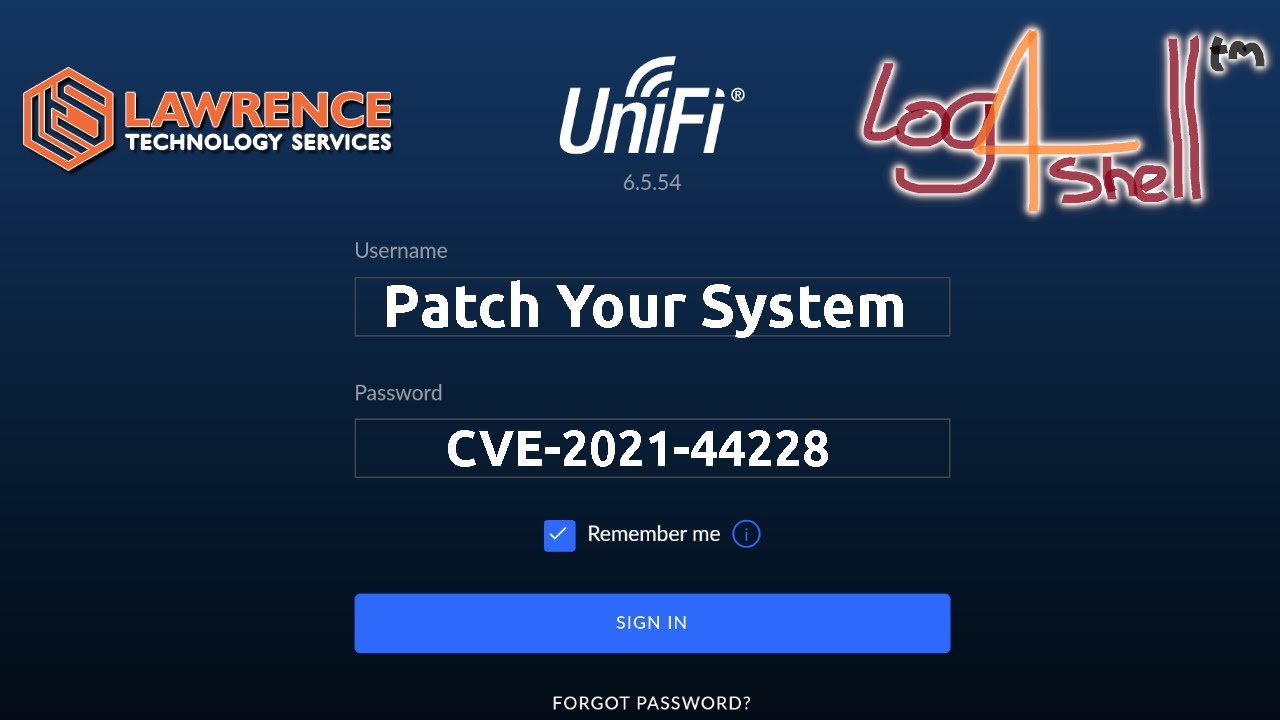
Dowload the updated controller here
https://community.ui.com/releases/UniFi-Network-Application-6-5-54/d717f241-48bb-4979-8b10-99db36ddabe1
Security bulletin
https://community.ui.com/releases/Security-Advisory-Bulletin-023-023/808a1db0-5f8e-4b91-9097-9822f3f90207?page=1
Reddit post about camera
https://www.reddit.com/r/Ubiquiti/comments/rfmmvb/log4j_attacks_from_unifi_cameras/
UI Forum post about camera
https://community.ui.com/questions/Log4j-RCE-attack-coming-from-UniFi-Cameras-G3Flex/5b36e14d-21cc-4214-ba1d-281ecee59a40
Tutorial on Graylog
Connecting With Us
- Hire Us For A Project: Hire Us – Lawrence Systems
- Tom Twitter
 https://twitter.com/TomLawrenceTech
https://twitter.com/TomLawrenceTech - Our Web Site https://www.lawrencesystems.com/
- Our Forums https://staging-forum.lawrencesystems.com/
- Instagram https://www.instagram.com/lawrencesystems/
- Facebook Lawrence Systems | Southgate MI
- GitHub lawrencesystems (Lawrence Systems) · GitHub
- Discord lawrencesystems
Lawrence Systems Shirts and Swag
►👕 https://teespring.com/stores/lawrence-technology-services
AFFILIATES & REFERRAL LINKS
Amazon Affiliate Store
![]() Lawrence Systems's Amazon Page
Lawrence Systems's Amazon Page
All Of Our Affiliates that help us out and can get you discounts!
![]() https://www.lawrencesystems.com/partners-and-affiliates/
https://www.lawrencesystems.com/partners-and-affiliates/
Gear we use on Kit
![]() Kit
Kit
Try ITProTV free of charge and get 30% off!
![]() Learn technology and pass IT certifications with ITProTV
Learn technology and pass IT certifications with ITProTV
Use OfferCode LTSERVICES to get 10% off your order at
![]() https://www.techsupplydirect.com/
https://www.techsupplydirect.com/
Digital Ocean Offer Code
![]() DigitalOcean | Cloud Hosting for Builders
DigitalOcean | Cloud Hosting for Builders
HostiFi UniFi Cloud Hosting Service
![]() HostiFi - UniFi Cloud Hosting
HostiFi - UniFi Cloud Hosting
Protect you privacy with a VPN from Private Internet Access
![]() Buy VPN with Credit Card or PayPal | Private Internet Access
Buy VPN with Credit Card or PayPal | Private Internet Access
Patreon
![]() lawrencesystems | creating Tech Tutorials & Reviews | Patreon
lawrencesystems | creating Tech Tutorials & Reviews | Patreon
![]() Timestamps
Timestamps ![]()
00:00 UniFi Controller 6.5.54
00:47 Log4J Attack Vectors
02:07 UniFi 6.5.54 Download
02:51 UniFi Protect Cameras
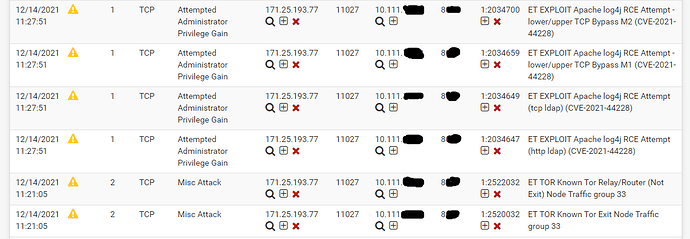
03:59 UniFi Indicators of Compromise
#UniFi #Log4j #Log4Shell