After wracking my brain for the entire day, I have not been able to figure out why the client cannot connect to the server is a Peer to Peer (Shared key) mode.
I followed this tutorial from the Opnsense documentation in addition to the Lawrence systems video on Site-2-Site VPN
I already have a working Road Warrior OpenVPN setup. I have both the opnsense boxes with me during set up. So I connected the client box to a port on my switch which is configured for a different VLAN. Since I am using a RFC1918 address as WAN IP for the client, I have also disabled the Block Private networks on the Server WAN interface. I disabled it on the client WAN interface as well just to be sure.
Here are my settings for the P2P:
Server:
Server Mode : Peer to Peer (Shared Key)
Protocol : UDP
Device Mode : tun
Interface : WAN
Local Port: 1195
Encryption algorithm: AES-256-CBC
Auth Digest Algorithm: SHA256
IPv4 Tunnel Network: 192.168.50.0/24
IPv4 Local Network : 192.168.1.0/24
IPv4 Remote Network: 192.168.3.0/24
Concurrent Connections: 3
Client:
Server Mode : Peer to Peer (Shared Key)
Protocol : UDP
Device Mode : tun
Interface: WAN
Remote Server:
Host: home.publicdomain.net Port: 1195
Shared Key : (copied from the server)
Encryption Algorithm: AES-256-CBC
Auth Digest Algorithm: SHA256
IPv4 Tunnel Network: 192.168.50.0/24
IPv4 Remote Network: 192.168.1.0/24Everything else is set to default.
on the Server, under Firewall–>Rules–>WAN, I opened port 1195
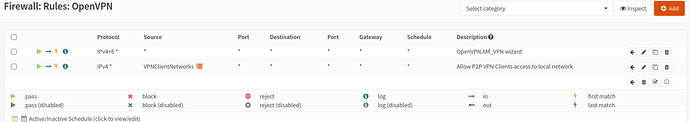
allow IPv4+6UDP * * WAN address 1195 * * Under Firewall–>Rules → OpenVPN – I already had the wide open rule created by the wizard (during my Road Warrior server setup)
On the Client, I created a wide open rule under Firewall–>Rules–>OpenVPN. I also assigned the ovpnc1 to an interface which created the relevant gateways. On the client the Outbound NAT is set to Automatic
However, whenever I initiate the connection, I see that the tunnel network is set on both the server and the client, but the dashboard keeps showing red for it. On the client, I checked the VPN–>Connection Status and it shows “waiting” for some time but on a retry it changes to “connecting” but never actually connects.
My log level is currently set to 3(recommended)
Here’s the client log:
2021-04-10T21:19:03 openvpn[8427] Restart pause, 5 second(s)
2021-04-10T21:19:03 openvpn[8427] SIGUSR1[soft,ping-restart] received, process restarting
2021-04-10T21:19:03 openvpn[8427] Inactivity timeout (--ping-restart), restarting
2021-04-10T21:18:03 openvpn[8427] UDP link remote: [AF_INET]84.xxx.xxx.xxx:1195
2021-04-10T21:18:03 openvpn[8427] UDP link local (bound): [AF_INET]10.100.100.47:0
2021-04-10T21:18:03 openvpn[8427] Socket Buffers: R=[42080->42080] S=[57344->57344]
2021-04-10T21:18:03 openvpn[8427] TCP/UDP: Preserving recently used remote address: [AF_INET]84.xxx.xxx.xxx:1195
2021-04-10T21:18:03 openvpn[8427] Preserving previous TUN/TAP instance: ovpnc1
2021-04-10T21:18:03 openvpn[8427] Re-using pre-shared static key
2021-04-10T21:18:03 openvpn[8427] NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
2021-04-10T21:17:58 openvpn[8427] Restart pause, 5 second(s)
2021-04-10T21:17:58 openvpn[8427] SIGUSR1[soft,ping-restart] received, process restarting
2021-04-10T21:17:58 openvpn[8427] Inactivity timeout (--ping-restart), restarting
2021-04-10T21:16:57 openvpn[8427] UDP link remote: [AF_INET]84.xxx.xxx.xxx:1195
2021-04-10T21:16:57 openvpn[8427] UDP link local (bound): [AF_INET]10.100.100.47:0
2021-04-10T21:16:57 openvpn[8427] Socket Buffers: R=[42080->42080] S=[57344->57344]
2021-04-10T21:16:57 openvpn[8427] TCP/UDP: Preserving recently used remote address: [AF_INET]84.xxx.xxx.xxx:1195
2021-04-10T21:16:57 openvpn[8427] Preserving previous TUN/TAP instance: ovpnc1
2021-04-10T21:16:57 openvpn[8427] Re-using pre-shared static key
2021-04-10T21:16:57 openvpn[8427] NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
2021-04-10T21:16:52 openvpn[8427] Restart pause, 5 second(s)
2021-04-10T21:16:52 openvpn[8427] SIGUSR1[soft,ping-restart] received, process restarting
2021-04-10T21:16:52 openvpn[8427] Inactivity timeout (--ping-restart), restarting
2021-04-10T21:15:52 openvpn[8427] UDP link remote: [AF_INET]84.xxx.xxx.xxx:1195
2021-04-10T21:15:52 openvpn[8427] UDP link local (bound): [AF_INET]10.100.100.47:0
2021-04-10T21:15:52 openvpn[8427] Socket Buffers: R=[42080->42080] S=[57344->57344]
2021-04-10T21:15:52 openvpn[8427] Preserving previous TUN/TAP instance: ovpnc1
2021-04-10T21:15:52 openvpn[8427] RESOLVE: Cannot resolve host address: home.publicdomain.net:1195 (Name does not resolve)
2021-04-10T21:15:31 openvpn[8427] Re-using pre-shared static key
2021-04-10T21:15:31 openvpn[8427] NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
2021-04-10T21:15:26 openvpn[8427] Restart pause, 5 second(s)
2021-04-10T21:15:26 openvpn[8427] SIGUSR1[soft,ping-restart] received, process restarting
2021-04-10T21:15:26 openvpn[8427] Inactivity timeout (--ping-restart), restarting
2021-04-10T21:15:16 openvpn[8427] MANAGEMENT: Client disconnected
2021-04-10T21:15:16 openvpn[8427] MANAGEMENT: CMD 'state all'
2021-04-10T21:15:16 openvpn[8427] MANAGEMENT: Client connected from /var/etc/openvpn/client1.sock
2021-04-10T21:14:26 openvpn[8427] UDP link remote: [AF_INET]84.xxx.xxx.xxx:1195
2021-04-10T21:14:26 openvpn[8427] UDP link local (bound): [AF_INET]10.100.100.47:0
2021-04-10T21:14:26 openvpn[8427] Socket Buffers: R=[42080->42080] S=[57344->57344]
2021-04-10T21:14:26 openvpn[8427] TCP/UDP: Preserving recently used remote address: [AF_INET]84.xxx.xxx.xxx:1195
2021-04-10T21:14:26 openvpn[8427] /sbin/route add -net 192.168.10 192.168.50.1 255.255.255.0
2021-04-10T21:14:24 openvpn[8427] /usr/local/etc/inc/plugins.inc.d/openvpn/ovpn-linkup ovpnc1 1500 1572 192.168.50.2 192.168.50.1 init
2021-04-10T21:14:24 openvpn[8427] /sbin/ifconfig ovpnc1 192.168.50.2 192.168.50.1 mtu 1500 netmask 255.255.255.255 up
2021-04-10T21:14:24 openvpn[8427] TUN/TAP device /dev/tun1 opened
2021-04-10T21:14:24 openvpn[8427] TUN/TAP device ovpnc1 exists previously, keep at program end
2021-04-10T21:14:24 openvpn[8427] ROUTE_GATEWAY 10.100.100.1/255.255.255.0 IFACE=igb0 HWADDR=90:e2:3f:ee:fd:ad
2021-04-10T21:14:24 openvpn[8427] Incoming Static Key Encryption: Using 256 bit message hash 'SHA256' for HMAC authentication
2021-04-10T21:14:24 openvpn[8427] Incoming Static Key Encryption: Cipher 'AES-256-CBC' initialized with 256 bit key
2021-04-10T21:14:24 openvpn[8427] Outgoing Static Key Encryption: Using 256 bit message hash 'SHA256' for HMAC authentication
2021-04-10T21:14:24 openvpn[8427] Outgoing Static Key Encryption: Cipher 'AES-256-CBC' initialized with 256 bit key
2021-04-10T21:14:24 openvpn[8427] NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
2021-04-10T21:14:24 openvpn[8427] MANAGEMENT: unix domain socket listening on /var/etc/openvpn/client1.sock
2021-04-10T21:14:24 openvpn[87354] library versions: OpenSSL 1.1.1k 25 Mar 2021, LZO 2.10
2021-04-10T21:14:24 openvpn[8427] Incoming Static Key Encryption: Cipher 'AES-256-CBC' initialized with 256 bit key
2021-04-10T21:14:24 openvpn[8427] Outgoing Static Key Encryption: Using 256 bit message hash 'SHA256' for HMAC authentication
2021-04-10T21:14:24 openvpn[8427] Outgoing Static Key Encryption: Cipher 'AES-256-CBC' initialized with 256 bit key
2021-04-10T21:14:24 openvpn[8427] NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
2021-04-10T21:14:24 openvpn[8427] MANAGEMENT: unix domain socket listening on /var/etc/openvpn/client1.sock
2021-04-10T21:14:24 openvpn[87354] library versions: OpenSSL 1.1.1k 25 Mar 2021, LZO 2.10
2021-04-10T21:14:24 openvpn[87354] OpenVPN 2.4.9 amd64-portbld-freebsd12.1 [SSL (OpenSSL)] [LZO] [LZ4] [MH/RECVDA] [AEAD] built on Jan 25 2021
2021-04-10T21:14:24 openvpn[87354] disabling NCP mode (--ncp-disable) because not in P2MP client or server mode
2021-04-10T21:14:24 openvpn[22639] SIGTERM[hard,init_instance] received, process exiting
2021-04-10T21:14:23 openvpn[22639] /usr/local/etc/inc/plugins.inc.d/openvpn/ovpn-linkdown ovpnc1 0 0 192.168.50.2 192.168.50.1 init
2021-04-10T21:14:23 openvpn[22639] Closing TUN/TAP interface
2021-04-10T21:14:23 openvpn[22639] /sbin/route delete -net 192.168.10 192.168.50.1 255.255.255.0
2021-04-10T21:14:21 openvpn[22639] MANAGEMENT: Client disconnected
2021-04-10T21:14:21 openvpn[22639] MANAGEMENT: CMD 'state all'
2021-04-10T21:14:21 openvpn[22639] MANAGEMENT: Client connected from /var/etc/openvpn/client1.sock10.100.100.0 is the WAN IP for my client opnsense box during testing…Once deployed, it will get it’s WAN from the ISP via DHCP. I have masked my public IP to 84.xxx and my public domain in the above log.
The gap in the log is until when the status is waiting…Then it seems to restart and then gets stuck in “connecting” status
and here’s the server log:
2021-04-10T10:49:03 openvpn[73113] MANAGEMENT: Client connected from /var/etc/openvpn/server3.sock
2021-04-10T10:48:01 openvpn[73113] MANAGEMENT: Client disconnected
2021-04-10T10:48:01 openvpn[73113] MANAGEMENT: CMD 'quit'
2021-04-10T10:48:00 openvpn[73113] MANAGEMENT: CMD 'status 2'
2021-04-10T10:48:00 openvpn[73113] MANAGEMENT: Client connected from /var/etc/openvpn/server3.sock
2021-04-10T10:46:58 openvpn[73113] MANAGEMENT: Client disconnected
2021-04-10T10:46:58 openvpn[73113] MANAGEMENT: CMD 'quit'
2021-04-10T10:46:58 openvpn[73113] MANAGEMENT: CMD 'status 2'
2021-04-10T10:46:58 openvpn[73113] MANAGEMENT: Client connected from /var/etc/openvpn/server3.sock
2021-04-10T10:45:56 openvpn[73113] MANAGEMENT: Client disconnected
2021-04-10T10:45:56 openvpn[73113] MANAGEMENT: CMD 'quit'
2021-04-10T10:45:56 openvpn[73113] MANAGEMENT: CMD 'status 2'
2021-04-10T10:45:56 openvpn[73113] MANAGEMENT: Client connected from /var/etc/openvpn/server3.sock
2021-04-10T10:44:54 openvpn[73113] MANAGEMENT: Client disconnected
2021-04-10T10:44:54 openvpn[73113] MANAGEMENT: CMD 'quit'
2021-04-10T10:44:54 openvpn[73113] MANAGEMENT: CMD 'status 2'
2021-04-10T10:44:53 openvpn[73113] MANAGEMENT: Client connected from /var/etc/openvpn/server3.sock
2021-04-10T10:43:51 openvpn[73113] MANAGEMENT: Client disconnected
2021-04-10T10:43:51 openvpn[73113] MANAGEMENT: CMD 'quit'
2021-04-10T10:43:51 openvpn[73113] MANAGEMENT: CMD 'status 2' I did notice that the times don’t match but that’s because the client will eventually be in a different timezone and the firewall is set up with that timezone. Not much info in the server logs. I have more than 100 pages of the same thing.
I also increased the log level on both client and server, but have not found out why the connection is not established. Have I missed some configuration? Can you please help me setup this Peer-2-Peer VPN connection?
Thanks,
Inxsible