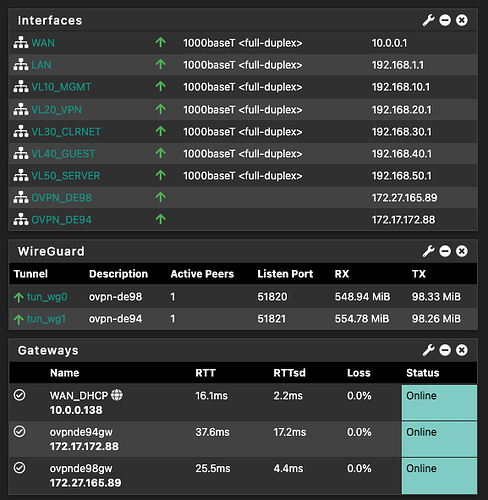
So I have recreated this guide exactly on pfsense plus 22.01 but used this video to implement wireguard instead of open vpn for vlan 20. Problem is that I somehow don’t have an internet connection even though the wireguard tunnels are definitely connected.
Would be nice if someone could point out what I missed, evrything else works fine
I have not done any testing using Wireguard wiht a privacy VPN service. If no one here has any suggestions might want to try the pfsense subreddit or the Netgate Forums.
I thought I’d ask here first, they’re not always very nice over there if you ask questions that in their opinion have a simple answer
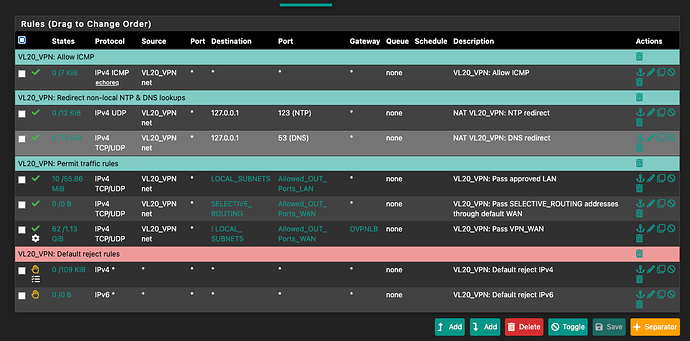
I’ve used this guide for firewall setup as well.
When i run into trouble, i temporarily convert the top allow icmp allow rule to allow all. If it starts working then the issue is in the rules (normally missing ports in the alias group), if not then the issue is normally configuration elsewhere. Note: always change it back after testing ![]()
If elsewhere ive got stuck on allowing the right ip addresses on my wireguard configs before, so similar connection starts but no traffic (a great reminder to document like i do at work when i had to figure it out the second time).
Hope this helps.
Thanks, I agree that going about problems that might have to do with firewall should be dealt with like you suggested. In this instance it doesn’t seem to be that easy. First thing I noticed when I looked at known bugs is that gateway monitoring seems to cause problems atm. So I disabled that and then put the allow all rule back in place. This seems to work kind of but not constantly, as the connection seems to come on and off frequently even though the wireguard connection itself seems to be stable. It might just be a problem with the wireguard implementation itself.
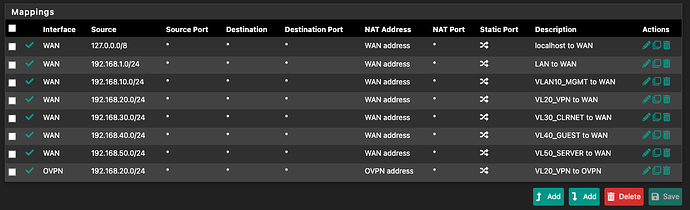
Is NAT configured? Was that updated?
NAT should beconfigured correctly. I’m getting an internet connection, it’s just not stable somehow. I suspect some combination of firewall rules and dns
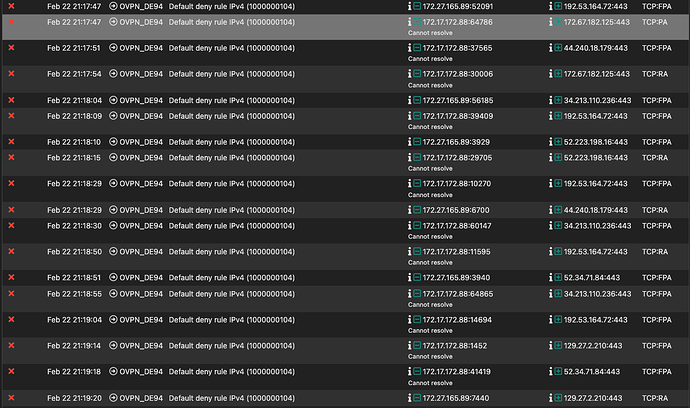
What do your gateway logs say?
Yep, this is indicating that you have something wrong with your configuration. It’s getting blocked by explicit deny, meaning that you don’t have an allow rule set up to allow your vpn tunneled devices to access the internet and what not.
The thing is that I have an allow all rout on all vg related Interfaces for testing, so I really don’t get why it’s blocked
Have you configured a wireguard vpn provider on your system @David?
Agreed. I think you need an exit node on your network to allow internet access.
Internet access is not the problem, the tunnel is working this is entirely caused by dns
Yes, I have. Did you create a new interface from your wireguard tunnel? Thus, rules set on the parent vg interface will not apply to the other vpn interface.