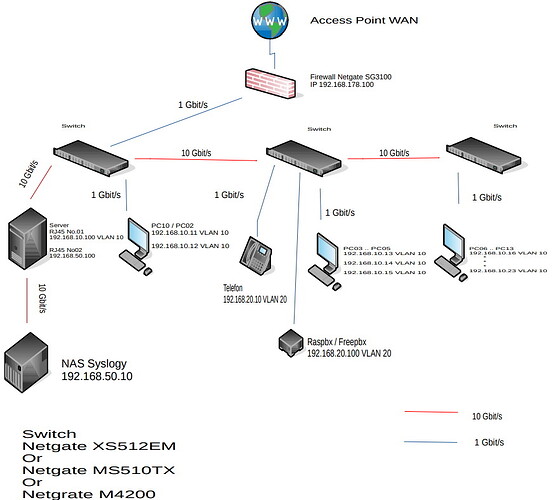
First, thank you for the diagram, it’s very helpful.
Just correcting your typo, you wrote Netgear, but I’m assuming you meant Netgate SG3100. The SG3100 only supports 1Gbps interfaces, though it looks like you can combine 4 of the switch-ports into a 2.5Gbps link (that’s assuming the connected switch supports the same).
I have a question about connectivity to the NAS, which appears to be on a unique network, 192.168.50.10/24? It appears that network is sitting behind a server that is dual homed. Will any of your clients need to connect to that NAS?
Based on your VLAN assignment, I’m going to assume that your pfSense config knows about each of the VLANs, and in that case the SG3100 is performing all the routing between network segments and is responsible for any of the firewall rules between those segments. I couldn’t find on Netgate’s website the actual performance of the SG3100. It’s possible you could start bottlenecking if you saturate those links (might be an edge use case)
E.g.:
If a PC needs Data from the Server. Goes the Routing?
a) PC → Switch → Server and retour or
b) PC → Switch → Firewall → Switch → Server and retour.
If you need data from the server that is hosted on the NAS, it really depends on where the data is being hosted. What I mean is, are clients pulling data directly from the NAS or is there some application layer hosting data on the server.
If you’re looking to support 10GBit links between those switches, then you’d need to go with the XS512EM switches as the others don’t support enough 10GBit interfaces to chain between.
IMO, I’d probably put the NAS on a dedicated 10Gbit port on the switch and (this would require testing) setup VLANs and some routing (Specific to the NAS) on the switch itself. That would keep the traffic out of the SG3100. Check out this article: Netgear VLAN Routing
I’d keep the SG3100 routing your public facing network traffic and any true zone to zone traffic. But for NAS traffic, it’s easy enough to let the switches route that traffic on it’s own (if it’s not a security concern). Remember, while the switch will let you route the traffic, it won’t perform any filtering (firewall) for that traffic. You would need to rely on the security of the NAS.