Hi all
I created a LinkedIn post about what I found a local ISP doing.
Can be found here:
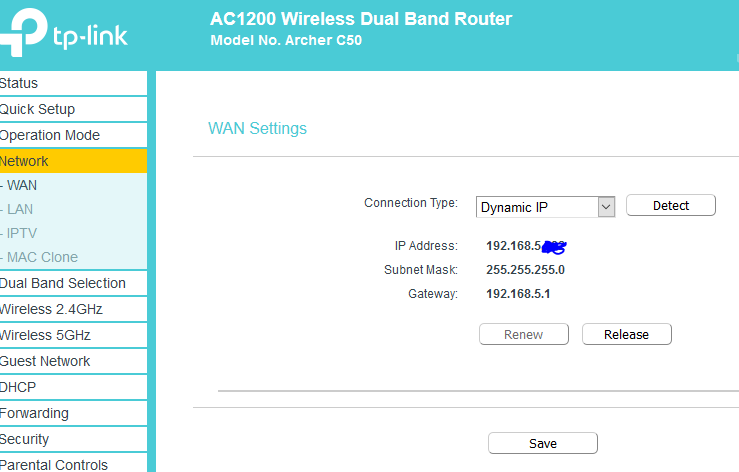
In a nutshell, I got a new client who got a brand new internet connection form a local ISP - I always check my client’s connections via external IP using sources such as Shodan for security reasons. Anyway sure as shit the ISP had port 6080 open on the connection - to which if you visited the external IP you could get to my client’s router login page. This is not good I thought.
As it turns out I have two or three more customers who have connections with the same ISP - Sure as shit again, port 6080 to these routers.
So I pinged them an email to basically ask if they could please turn off port 6080 to my client’s connection. This is the reply I git from the helpdesk.
Hi Chris,
We do appreciate your concern, but the router is secured with custom credentials and the default credentials do not exist on the router.
Also, for the benefit of the customer, remote management is enabled to allow us to remotely assist with any WiFi issues, port forwarding, etc.
OK so I got on my high horse a bit here - this was the reason for my LinkedIn post - I find out today that the ISP wants a meeting with me tomorrow and they had a guy onsite at my client and he was acting a bit cagey and trying to find out who I was - and was assuring my client that the network is absolutely secure and always has been.
Now, 6080 was giving me router login pages that should not be exposed in the first place - but also bearing in mind that the port was just a redirect of ‘port 80’ not ‘443’ therefore an unencrypted connection.
So, before I go for the meeting tomorrow, am I absolutely wrong and this is a fine way to operate or am I going in over my head telling these guys they are wrong and that they need to secure there shit.
Since the ISP is asking around about who I am (I’m an MSP located in the same City) I want to get my facts absolutely sure and that I am 100% correct in what I am implicating.
The routers in question where Asus and TPLink. If anyone can point me to some CVE’s or known credential exploits it would be greatly appreciated!
Thanks - please ask for more info if you need it or whether I have not made myself clear. Also, tell me if I am being an ass.
Attached is the interface I could access that belongs to one of my clients, over port 6080.
Thanks all.