Great Video, I have been searching for a video like this forever as i was trying to set this up for myself.
i have been watching your videos for a long time and am a huge fan.
I do have a comment about the flow of the video, while i was able to understand what you were talking about since i spent a long time reading up on this topic, i feel compared to your previous video on other topics (which are excellent as a follow along and very well structured even for someone completely new) I feel this was not as well structured.
I mean the content excellent, it just need a bit more introduction and preface before you got into the meat of things.
More along the lines, why one would need this, what alternatives are available out there.
Most of your videos before you get started with the topic you explain what the topic is, what alternatives are available (which i love because then i can go out and read up on those topics as well and is a great way of learning new things.
Maybe do another video just talking about those points before we start watching this video.
Nonetheless this is an excellent video. keep it up.
Thanks for the feedback, it’s always challenging to figure where to start on the topic, but I figured the average user is not searching for HA Proxy so this video was more advanced. I could have easily added another 30 minutes to the video but I figured it was long enough. ![]()
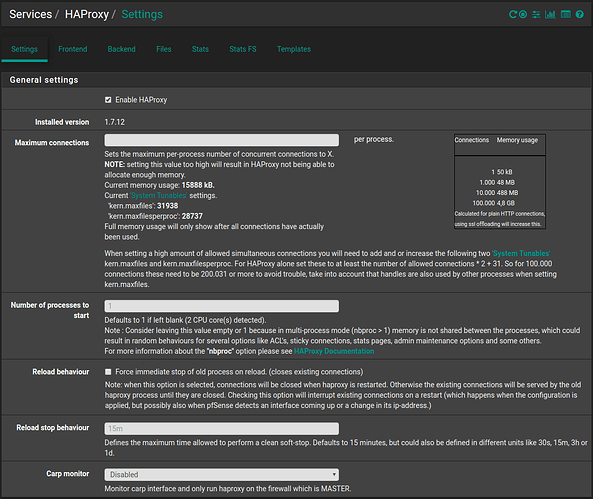
What about the settings page for HAproxy?
I assume we should click the enable checkbox. What about the maximum connections? Specifically, for the SG-1100 used in the video?
Thanks,
Willie
You make a fair point.
maybe a follow up video??? ![]()
Yes, @maddoxw it does have to be enabled to work. I am not sure what the max connections the sg1100 could handle, but probably not a lot.
I tried a range of values between 10 and 200,000, but I always get same warning after each save.
If I disable the frontend, the warning goes away.
That is because the error message is telling you to adjust the “Max SSL Diffie-Hellman size” under tuning further down on that page, not the max number of connections.
Awesome Tom, That did it. I totally missed that.
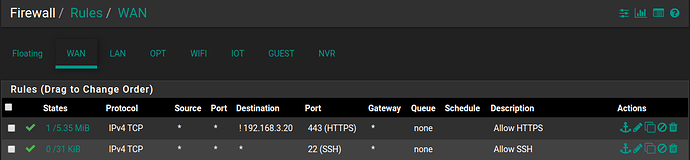
Now everything works great EXCEPT I can still bring up the login screen to my FreeNAS from outside my LAN. My WAN firewall rule for port 443 is configured as follows:
Do you know why doesn’t this work?
Thanks,
-W
The destination should be “This Firewall”
Great video! I used this to setup ssl offloading for various servers but notice now that all sever logs now just show requests coming from pfsense firewall instead of the actual client’s IP. I have tried using the “Transparent Client IP” option on backends for HAProxy, but setting that option breaks the proxying. I noticed the warning about this setting preventing clients on the same LAN from connecting … which is what I am using HAproxy to do. Is it possible to pass internal LAN client IPs through HA Proxy while it also performs SSL offloading? Hopefully, my first post is somewhat coherent ![]()
I don’t think there is a way to do that, but you could just pull the logs from HAProxy instead of the applications that are running behind it.
Ok…Thanks for the quick followup Tom. Love your youtube channel. Impressed how you are able to juggle that with running your business!
Hey Tom!
Thanks for a great and detailed explanation video on how to set this all up! However I actually couldn’t get it to work. I followed all your instructions exactly, but the sites refuse to open. Important point to note in my setup is I’m behind a CGNAT. So where you get a public IP, I get a private WAN IP in the 10 series. Is there any way all this can still work behind a CGNAT? When outside, I use ZeroTier to remote in. Just want proper certificates to get rid of the self signed certificates hassle.
Yes, you should be using an internal IP address and unless the systems from outside the network using ZeroTier are using your DNS, you may have to use host entries.
Sorry, didn’t understand the first part. Where and how exactly do I specify an internal IP? And no, not setup any DNS in ZeroTier. At least I don’t think I did! Just installed ZT and joined Network using zerotier-cli, that’s it.
The internal IP address on your pfsense.
Hi Tom,
I was looking for this. THANK YOU.
I tried to adapt your video to my setup. Here in France, my isp gave me a router that does not allow bridge mode, so my SG1100 is in the DMZ.
I have a digicert certificate with my domain.
What I don’t know is how to setup my frontend.
I created the A record, and they are pointing to my isp router’s IP.
Do I have to expose my pFsense wan IP, so the A records will see the firewall?
Thank you.
JJ
If you want services publicly available on your pfsense, then you have to either have a public WAN ip or forward ports from the firewall in front of it that does to your pfsense.
I need large amounts of help lol.
I followed your instructions exactly but can only access my addresses internally. External DNS points to router WAN and firewall rules are exactly like yours.
I do not have NAT Reflection on but I have toggled it to see if it would help.
I am at a loss and do not even understand how the proxy only works for me internally.