Hey @LTS_Tom, First let me start off by saying Thank You! Your YouTube channel has provided me the confidence to truly embrace the learning process with pfSense. Although I’m still learning and just scratching the surface with most things, not only have I started a home lab journey but I’ve been able to support my team at work with architecting, deploying and supporting a test environment that we use to build complex software integrations for commercial building automation. It spans 3 offices now! And I’m the sales guy 
That said, I’ve been stumped…. I built 3 HAProxy FrontEnds on my home lab pfSense. Two of them use the same WildCard Cert. One listens on WAN port 443, another on the LAN port 443. The last one is a port 80 redirect that listens on WAN and LAN port 80 and only modifies the scheme to https.
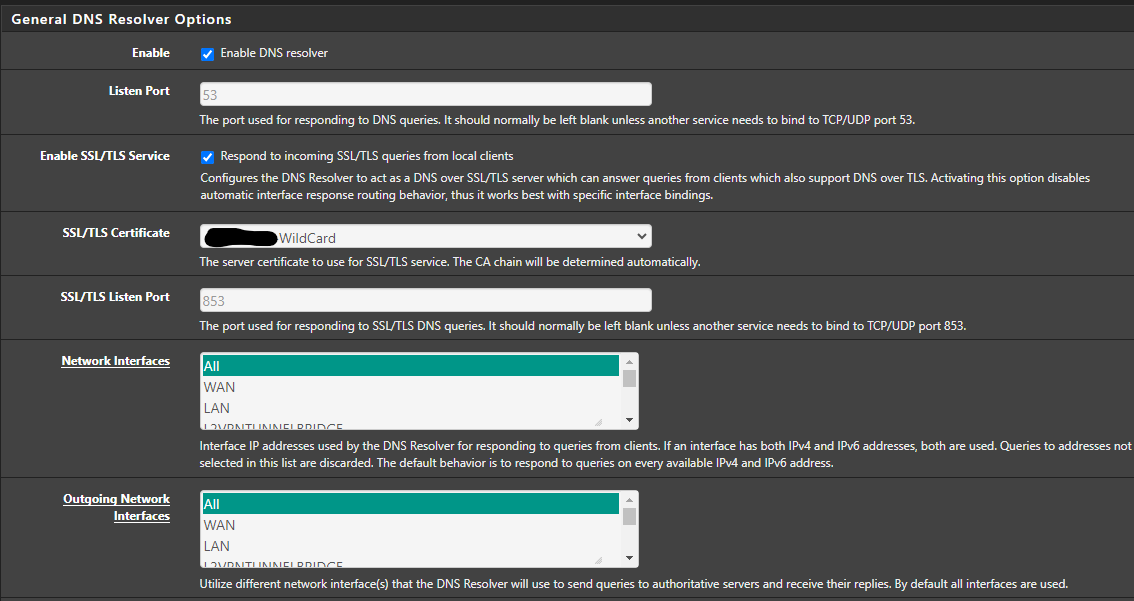
Here is where things get weird. This setup was stable for 6mo maybe a year. Recently, like a week or so ago, some local PCs in my house that use the DNS overrides for the internal sites are using the WAN port 443 instead. I get a 503 error because the BackEnds don’t exist on WAN. So, naturally in my testing, I disabled both the port 80 redirect and the WAN Front End to which on the failing PC, I get a TimeOut error. So… I thought to myself, why would it all the sudden stop listening on LAN 443. I’ve completely reinstalled pfSense and created separate certs now in my attempts but whatever I do, some PCs (Windows 11 and macOS) fail to use the LAN port even though the DNS Overrides exist and work on at least one PC.
Could it be something wrong with DNS or is it that you shouldn’t use the same wild card cert on WAN and LAN??
The only other tidbit of trouble shooting I have is that the log on GrayLog shows some handshake errors but also shows that it’s coming from the WAN side.
Maybe a DNS flush on the client PCs?
Thoughts? Anyone one else run into this weird one?
One other thought I had was to change my wild card cert from *.example.com to two
*.pub.example.com
*.pri.example.com
That way the OS won’t cache the wrong addresses, think it knows where to go and fail to request the DNS Override entry???
Okay… So buit more information.
Here is an nslookup from one of the Windows PC’s that’s failing:
PS C:\Users\Pogo> nslookup -debug truenas.example.ca 192.168.69.1
------------
Got answer:
HEADER:
opcode = QUERY, id = 1, rcode = NOERROR
header flags: response, auth. answer, want recursion, recursion avail.
questions = 1, answers = 1, authority records = 0, additional = 0
QUESTIONS:
1.69.168.192.in-addr.arpa, type = PTR, class = IN
ANSWERS:
-> 1.69.168.192.in-addr.arpa
name = pfSense.branya.lan
ttl = 3600 (1 hour)
------------
Server: pfSense.branya.lan
Address: 192.168.69.1
------------
Got answer:
HEADER:
opcode = QUERY, id = 2, rcode = NOERROR
header flags: response, want recursion, recursion avail.
questions = 1, answers = 1, authority records = 0, additional = 0
QUESTIONS:
truenas.example.ca.example.ca, type = A, class = IN
ANSWERS:
-> truenas.example.ca.example.ca
internet address = XXX.XXX.XXX.XXX [PUBLIC IP ADDRESS]
ttl = 971 (16 mins 11 secs)
------------
Non-authoritative answer:
------------
Got answer:
HEADER:
opcode = QUERY, id = 3, rcode = NOERROR
header flags: response, want recursion, recursion avail.
questions = 1, answers = 0, authority records = 1, additional = 0
QUESTIONS:
truenas.example.ca.example.ca, type = AAAA, class = IN
AUTHORITY RECORDS:
-> example.ca
ttl = 827 (13 mins 47 secs)
primary name server = ns1.digitalocean.com
responsible mail addr = hostmaster.example.ca
serial = 1699331276
refresh = 10800 (3 hours)
retry = 3600 (1 hour)
expire = 604800 (7 days)
default TTL = 1800 (30 mins)
------------
Name: truenas.example.ca.example.ca
Address: XXX.XXX.XXX.XXX [PUBLIC IP ADDRESS]
PS C:\Users\Pogo>
And here is an nslookup from a linux machine that directs properly:
pogo@dockerhub:~$ nslookup -debug truenas.example.ca 192.168.69.1
Server: 192.168.69.1
Address: 192.168.69.1#53
------------
QUESTIONS:
truenas.example.ca, type = A, class = IN
ANSWERS:
-> truenas.example.ca
internet address = 192.168.69.1
ttl = 3600
AUTHORITY RECORDS:
ADDITIONAL RECORDS:
------------
Name: truenas.example.ca
Address: 192.168.69.1
------------
QUESTIONS:
truenas.example.ca, type = AAAA, class = IN
ANSWERS:
AUTHORITY RECORDS:
ADDITIONAL RECORDS:
------------
pogo@dockerhub:~$
Let me know if there is a log or something more that I can provide. (I’ve done DNS flushing everywhere to see if that helped. It didn’t.)
 https://twitter.com/TomLawrenceTech
https://twitter.com/TomLawrenceTech![]() Lawrence Systems's Amazon Page
Lawrence Systems's Amazon Page![]() https://www.lawrencesystems.com/partners-and-affiliates/
https://www.lawrencesystems.com/partners-and-affiliates/![]() Kit
Kit![]() Tech Supply Direct - Premium Refurbished Servers & Workstations at Unbeatable Prices
Tech Supply Direct - Premium Refurbished Servers & Workstations at Unbeatable Prices![]() DigitalOcean: AI-Powered Unified Inference Cloud Infrastructure
DigitalOcean: AI-Powered Unified Inference Cloud Infrastructure![]() HostiFi - Fast and Reliable UniFi in the Cloud
HostiFi - Fast and Reliable UniFi in the Cloud![]() https://www.privateinternetaccess.com/pages/buy-vpn/LRNSYS
https://www.privateinternetaccess.com/pages/buy-vpn/LRNSYS![]() https://www.patreon.com/lawrencesystems
https://www.patreon.com/lawrencesystems![]() Time Stamps
Time Stamps ![]()
![]() HAProxy on pfsense
HAProxy on pfsense![]() How The HAProxy Reverse Proxy Works
How The HAProxy Reverse Proxy Works![]() pfsene packages and WebConfigurator settings
pfsene packages and WebConfigurator settings![]() ACME Let’s Encrypt Setup
ACME Let’s Encrypt Setup![]() Setting Up HAProxy General Settings
Setting Up HAProxy General Settings![]() Creating HAProxy Backend
Creating HAProxy Backend![]() Creating HAProxy Frontend
Creating HAProxy Frontend![]() DNS Settings & Host Override Setup
DNS Settings & Host Override Setup