Hi all
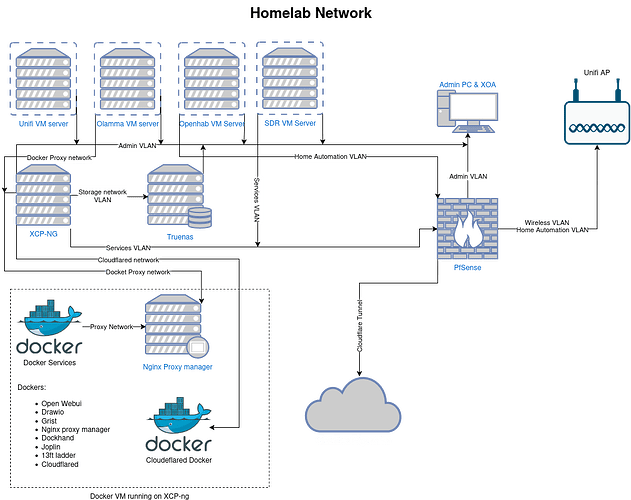
I am looking to created a Home lab network. Below is the proposed configuration. My goal is to create isolation between networks for security, specialty dockers separate from the admin network and also allow access of docker service to selected networks.
any advice would be helpful.
I don’t see what switch you are using but for this to work you would create VLAN / Networks on pfsense and on the switch along with the rules to keep things separate.
1 Like
Its a bit hard for me to read everything on that diagram, but I get a sense you may have too many VLANs. You will want to take into consideration that inter-VLAN routing can slow down your network traffic. I really only have four VLANs in my home lab: My trusted VLAN, a “server” VLAN which is un-trusted or almost a DMZ network. Anything that faces the internet goes in that VLAN. I also have a VLAN that all my device management interfaces sit on, and a non-routed storage VLAN. That last one is kind of unique. It only exists at Layer 2, that is to say in my switch. All of the IPs are hard coded, and pfSense has no record of this VLAN. I actually have two NICs in all my servers and NAS devices, and the second port is dedicated to this VLAN.
NOW that is not to say I don’t have other VLANs, but these serve my home more than my home lab. I have an IoT VLAN and a guest VLAN, which is where my kids devices live.
Hi Tom
I tried to just represent the VLAN’s to reduce confusion. The VLAN’s will be created on the switch.
Hi Louie
When you say you have a Server VLAN, does this run Docker/VMs?
I plan to route some of the services/Docker through Cloudflare tunnels, and some through to Admin and Wireless, since this only opens port 443 and presents a limited attack surface for any hacker to exploit. As my setup is modest, inter-VLAN routing would not have a huge effect on network traffic.
I have a non-routed Storage and Home Automation VLAN connected to an SSID that is routed only for NTP, and in the future, OpenHAB or Home Assistant would be added to this VLAN.
My Truenas has 2 NICs: 1 x 2.5 Gbps for storage, 1 x 1 Gbps for management. The NAS is under spec for the 2.5 Gbps NIC, so throughput on the storage VLAN isn’t great.
The XCP-ng server has only 1 x 2.5 Gbps NIC, with Storage and management on separate VLANs.
The Cloudflare and Docker networks are just Docker networks that I plan to connect to the services VLAN.
I run VMs and Docker containers on both my trusted network and my server network. The difference being the ones on my server network are exposed via cloudflare tunnels. I don’t open any ports on my firewall. I run three wordpress websites and a discourse forum, that all are exposed via cloudflare tunnels. Services that don’t go out to the internet, like my Grafana stack, Vaultwarden, SearXNG, etc. live on my trusted VLAN, and if I need to access them when away form home, I do it via Tailscale.