I am running a couple of websites configured as described in this article from LEVEL1Techs forum. I am running haproxy on my Linode with Let’s Encrypt and routing the traffic back to my home IP address. At home I have individual ports opened on the firewall that allow that traffic in and then I route that traffic to specific local IP addresses with HAproxy. I believe that I have https traffic working up to my WAN but then inside the network it is unencrypted. I have tried to configure haproxy to provide certificates to also encrypt the internal traffic but I have been unsuccessful. My first question is can Haproxy route the traffic without removing the encryption coming from the Linode or is essential that I provide certificates within my network? When I have SSL offloading unchecked on the front end and Encrypt(SSL) unchecked on the backed it all works. But I believe in this case the internal traffic is unencrypted. If I change both of those settings to how it seems they should be I get a 502 Bad Gateway error. I hope I described all this clearly enough. I am self taught so I appreciate your understanding with the fact that I don’t phase things correctly.
This is what I am assuming your goal is:
Server Encrypted Traffic with Self Signed Cert → Your Firewall → Linode HAProxy → Site Encrypted with LE Cert
Traffic from the individual servers to HAProxy would not be encrypted unless you have those servers setup to us encryption. When / if you do setup encryption on those servers HAProxy can be set to access self signed certs.
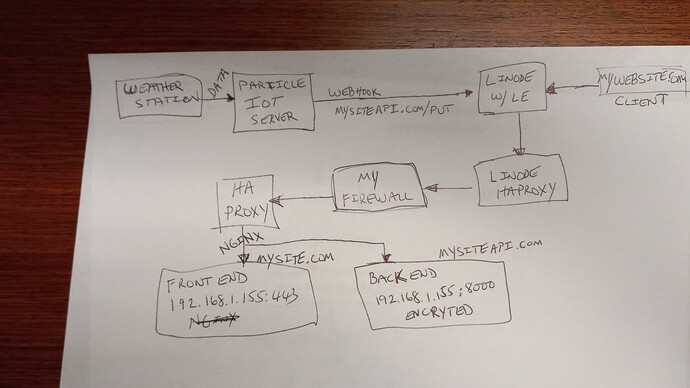
Thanks. One thing that got me confused in the video was the term Self Signed Cert. I assume that the certs I generate in pfsense using the api key from my domain provider are not self signed. Since lets encrypt uses the domain for verification. Is this correct? I included a picture of what I am doing. I believe the part I am missing, or that doesn’t work, is the encryption for 192.168.1.155. I suppose I should say that I understand this isn’t how things are normally done. I have a freenas server and the main reason I am hosting things is so that I can store the weather data on the freenas drive. There is going to be very little use of the site.
Yes, HAProxy can be configured to use a Let’s encrypt certificate.
@theaddies , yep. Just be sure you use acme in pfsense to obtain that cert. Then reference it from HA proxy settings.
OK, thanks. That is what I am doing. The thing that I have not done is installed a certificate on the machine for the front end and back end. When I was testing things out it seemed as though I had an incomplete encryption chain. When testing the API the browser I was using refused to transfer data because it said part of the route was unencrypted. I assumed this was the route from nginx to 192.168.1.155. To encrypt that step I believe I need to modify the nginx.conf file to route through 443 for the frontend and 8000 for the back end with both routes having certificates. Is this correct reasoning? Thanks again.