This tutorial was created and tested using Ubuntu 20.10 on Digital Ocean. It will likely work fine with other distributions but some modifications may be needed.
Server Side Setup
Create new droplet using Ubuntu 20.10 and choose the region you prefer.
Log into server and make sure system is up to date
apt-get update && apt-get upgrade
Reboot if there are update that require it
Optional: customize the shell settings
git clone https://github.com/lawrencesystems/dotfiles.git
cd /root/dotfiles/
Run the install.sh
Next we need to enable IP Forwarding. IP forwarding is the ability for an operating system to accept incoming network packets on one interface, recognize that it is not meant for the system itself, but that it should be passed on to another network. Edit the file /etc/sysctl.conf and change and uncomment to the line that says net.ipv4.ip_forward=1
Now reboot or run sysctl -p to activate the changes.
Install wireguard
apt-get install wireguard
Go to to the Wireguard config cd /etc/wireguard and then run the following command to generate the public and private keys for the server.
umask 077; wg genkey | tee privatekey | wg pubkey > publickey
The run cat privatekey and copy it so we can put it in to the server config file.
Create the /etc/wireguard/wg0.conf
vim /etc/wireguard/wg0.conf
This will get the basic server side setup and we will be coming back to this file to add the peers later.
[Interface]
PrivateKey = <Your Private Key Goes Here>
Address = 192.168.69.1/24
ListenPort = 51820
PostUp = iptables -A FORWARD -i wg0 -j ACCEPT; iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
PostDown = iptables -D FORWARD -i wg0 -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE
To test that the server works run wg-quick up wg0 to bring up the interface. Running wg-quick down will bring the interface down.
If you want the wg0 interface to be active on boot you need to run
systemctl enable wg-quick@wg0
Then you can use to systemctl start wg-quick@wg0 start the server, systemctl stop wg-quick@wg0 stop the server and systemctl status wg-quick@wg0 to check the status.
Linux Client Side Setup
Install wireguard
apt-get install wireguard
Go to to the Wireguard config cd /etc/wiregaurd and then run the following command to generate the public and private keys for the server.
umask 077; wg genkey | tee privatekey | wg pubkey > publickey
The run cat privatekey and copy it so we can put it in to the server config file.
Create the /etc/wireguard/youtube.conf
vim /etc/wireguard/youtube.conf
[Interface]
PrivateKey = <Your Private Key Goes Here>
Address=192.168.69.2/24
Run wg-quick up youtube to make sure the system comes up and run wg-quick down youtube to take down the interface.
Getting the Wireguard Systems Talking
On the Ubuntu Digital Ocean server edit /etc/wireguard/wg0.confand add the peer information
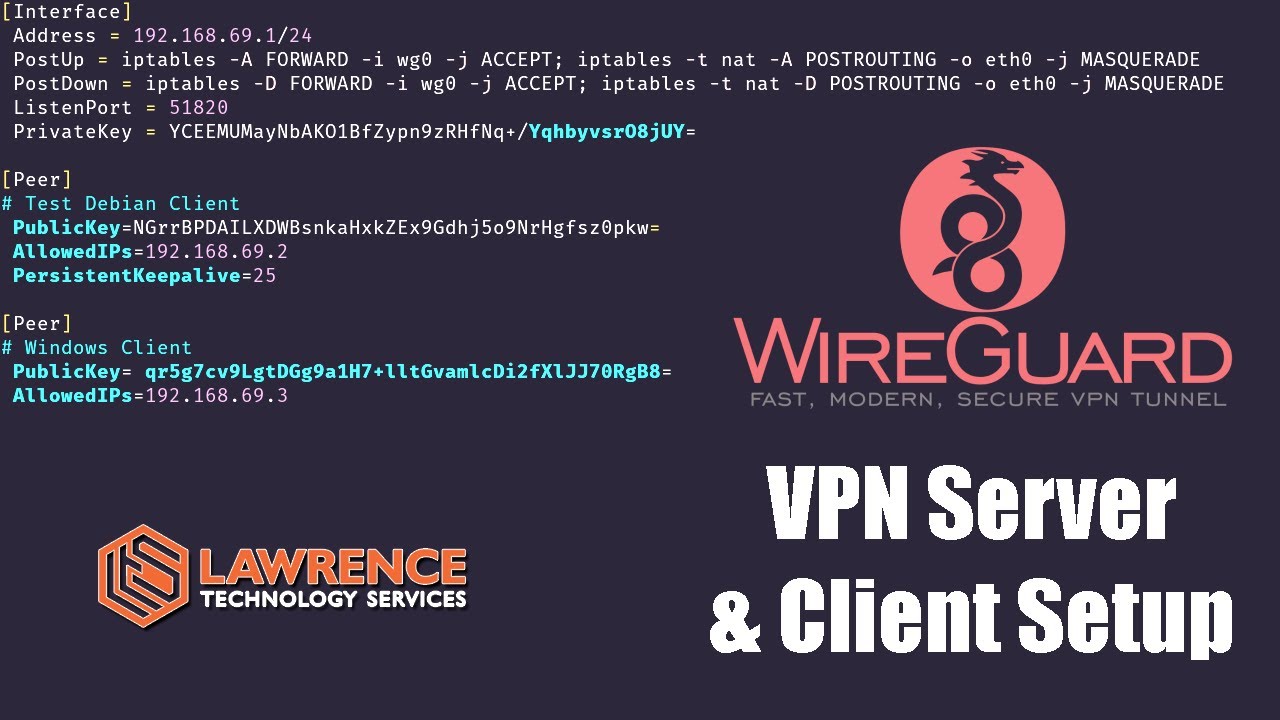
[Interface]
Address = 192.168.69.1/24
PostUp = iptables -A FORWARD -i wg0 -j ACCEPT; iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
PostDown = iptables -D FORWARD -i wg0 -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE
ListenPort = 51820
PrivateKey = <This Ubuntu Servers Private Key>
[Peer]
# Test Debian Client
PublicKey=<The Public Key of the Debian Client>
AllowedIPs=192.168.69.2
PersistentKeepalive=25
On the Debian linux client edit /etc/wireguard/youtube.confand add the peer information
[Interface]
PrivateKey = <This Debian Client Private Key Goes Here>
Address=192.168.69.2/24
[Peer]
# Ubuntu Digital Ocean Server
PublicKey=<Public Key From Ubuntu Digital Ocean Server>
Endpoint=<Public IP of Ubuntu Digital Ocean Server>:51820
AllowedIPs = 0.0.0.0/0 # Forward all traffic to server
Once both sides have been complete and Wireguard restarted on both side the system should be able to communicate. You can first test from the Debian Client by running ping 192.168.69.1 to make sure the tunnels are working and then try getting out the internet by running ping 1.1.1.1 on the Debian and confirm response.
Turning on the UFW firewall on the server
It is easy to enable the UFW firewall there are a few ports we need to open first, port 22 TCP for ssh management and 51820 UDP for Wireguard. To do this simply:
ufw allow 22/tcp
ufw allow 51820/udp
ufw enable
Add other or change ports if needed for your configuration.