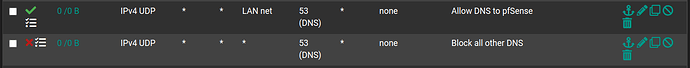
I noticed in many of the videos which show DNS firewall rules, that the Allow rule Destination is set to LAN net and that both the Allow and Deny rule are UDP only. For example, see “How To Setup VLANS With pfsense & UniFI. Also how to build for firewall rules for VLANS in pfsense” around timestamp 7:00
Specifically,
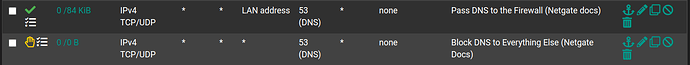
I’ve also seen the DNS firewall rules with Allow Destination → LAN Address and both on TCP/UDP:
In what situations is it best to use the first set over the second set and vice versa?
Thanks
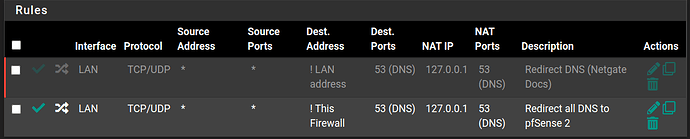
If you want to redirect DNS not just block it from going outside, this guide is for that pfSense Configuration Recipes — Redirecting Client DNS Requests | pfSense Documentation
Sooo, If I add DNS redirection as per the recipe, I should choose the “LAN net” option? I’m not sure how this answers my question.
DNS for most devices is UDP but there are situations where it can request over TCP
That makes sense. For the Redirect rule, I noticed that you have used “!This Firewall” as Dest Address in some of your videos, but the Netgate docs use “!LAN address”.
Is there a reason to prefer one over the other?
The Netgate way is the correct way.
Roger Netgate way. Do we need to set up this port forwarding rule for each vlan?
Yes, for each internal subnet / network segment.