Hi,
I’d like to convert flat network spanning two locations into VLANS.
I came across this video on https://www.youtube.com/watch?v=ptqa7JXbS5U and wanted to do something similar on a network I sometimes help out with for a friend.
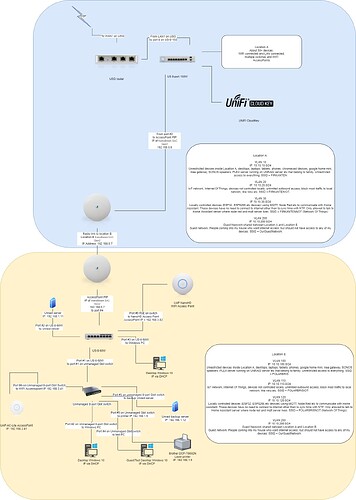
That network connects two locations (buildings) with 2 x Ubiquiti NanoBeam 5AC Gen2 devices.
The entire network is set up as a single flat 192.168.0.0/22 network with a netmask of 255.255.252.0 giving us 4 ‘networks’,
192.168.0.1 - 254 → primarily used on Location A
192.168.1.1 - 254 → primarily used on Location B
192.168.2.1 - 254 → primarily used on Location A
192.168.3.1 - 254 → used on Location A and Location B for all DHCP connected devices
When the network was initially installed several years ago, no VLAN’s was set up, and everything was one network, one broadcast domain covering both buildings.
The network started with one ASUS RT-N66U router, and was upgraded to a USG router a couple of years ago, one unifi 8-port 150 switch, two AC PRO Access points and two NanoBeam 5AC Gen2 to connect the two locations. There is also a number of small 5-port and 8-port dumb switches in both Location A and B.
This was just fine when it was first installed several years ago, but as time have passed, more and more devices have been connected in both Location A and Location B.
Now we want to separate the two locations into VLAN’s in order to limit broadcast traffic.
Attached is a PDF with current network topology, with IP addresses of the most important devices in both locations.
Ideally, here is a brief summary of how we would like to segment the network at both locations:
Location A:
VLAN 10
IP: 10.10.10.0/24
Unrestricted devices inside Location A, desktops, laptops, tablets, phones, chromecast devices, google home mini, ikea gateway, SONOS speakers, PLEX server running on UNRAID server etc that belong to family. Unrestricted access to everything. SSID = LOCATIONA
VLAN 20
IP: 10.10.20.0/24
IoT network, Internet Of Things, devices not controlled locally, unlimited outbound access, block most traffic to local network, like roku etc. SSID = LOCATIONAIOT.
VLAN 30
IP 10.10.30.0/24
Locally controlled devices (ESP32, ESP8266 etc devices) using MQTT, Node Red etc to communicate with Home Assistant in Location A. These devices have no need to connect to internet other than to sync time with NTP. Only allowed to talk to Home Assistant server where node red and mqtt server lives. SSID = LOCATIONANOT (Network Of Things)
Location B:
VLAN 100
IP: 10.10.100.0/24
Unrestricted devices inside Location B, desktops, laptops, tablets, phones, google home mini, ikea gateway, SONOS speakers, PLEX server running on UNRAID server etc that belong to family. Unrestricted access to everything. SSID = LOCATIONB
VLAN 110
IP: 10.10.110.0/24
IoT network, Internet Of Things, devices not controlled locally, unlimited outbound access, block most traffic to local network, like roku etc. SSID = LOCATIONBIOT.
VLAN 120
IP 10.10.120.0/24
Locally controlled devices (ESP32, ESP8266 etc devices) using MQTT, Node Red etc to communicate with Home Assistant in location B. These devices have no need to connect to internet other than to sync time with NTP. Only allowed to talk to Home Assistant server where node red and mqtt server lives. SSID = LOCATIONBNOT (Network Of Things)
VLAN 200
IP 172.16.200.0/24
Guest Network shared between Location A and Location B
People coming into any of location A or location B who want internet access, but should not have access to any other devices. SSID = OurGuestNetwork
All devices in VLAN 10 and VLAN 100 needs to talk to each other, e.g. UNRAID servers in both locations, PLEX and media servers etc in both locations while still being in separate broadcast domains.
I have never created any VLANS before, and have tried to read up on how to set it up, and think that I have a good understanding.
At the moment, I just have three questions that I do not know how to solve:
-
How do I assign IP-addresses to the two NanoBeam 5AC Gen2 devices to connect the two locations? How do I set up the ports they are connected to, the UniFi Switch 8-150W on location A and the UniFi Switch 8 60W on location B?
-
Somewhere I read that it is only possible to set up 4 SSID’s on the Unifi CloudKey Controller. How do I solve my plan of using a total of 7 SSID’s for the complete setup? Do I really need 7 SSID’s? Is there other ways of achieving the goal of separating out stuff?
-
For some of the ESP32 and ESP8266 devices it is desirable to force connection to one specific access point, the access point I know for sure is the closest. Is it possible for an access point to both be accessable by the general SSID and also a specific SSID for that access point? Is there a better way to force connection to a specific access point?
I am also open to other ways of rearranging the current network.
The primary goal is to separate the two locations into their own VLAN’s, and to make it as secure as possible within reason.
I would appreciate if anyone could point me to some information on how to achieve what I have described above and in the attached image.