Additional Resources:
Wireguard Device Access Video
Lab video
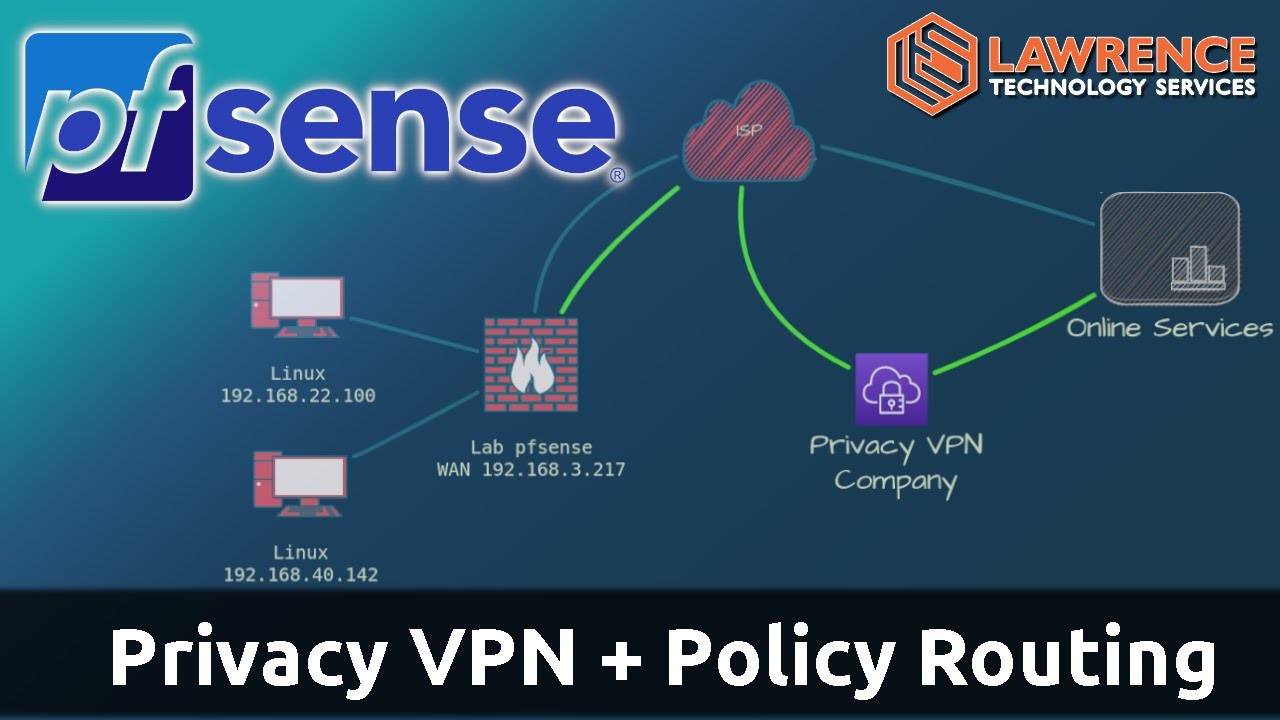
pfsense Privacy VPN video
Connect With Us
- Hire Us for a project: Hire Us – Lawrence Systems
- Toms’ Twitter
 https://twitter.com/TomLawrenceTech
https://twitter.com/TomLawrenceTech - Our Website https://www.lawrencesystems.com/
- Our Forums https://forums.lawrencesystems.com/
- Instagram https://www.instagram.com/lawrencesystems/
- Facebook https://www.facebook.com/Lawrencesystems/
- GitHub lawrencesystems (Lawrence Systems) · GitHub
- Discord Lawrence Systems
Lawrence Systems Shirts and Swag
AFFILIATES & REFERRAL LINKS
Amazon Affiliate Store
![]() Lawrence Systems's Amazon Page
Lawrence Systems's Amazon Page
UniFi Affiliate Link
![]() Ubiquiti Store
Ubiquiti Store
All Of Our Affiliates help us out and can get you discounts!
![]() Partners We Love – Lawrence Systems
Partners We Love – Lawrence Systems
Gear we use on Kit
![]() Kit
Kit
Use OfferCode LTSERVICES to get 10% off your order at
![]() Tech Supply Direct - Premium Refurbished Servers & Workstations at Unbeatable Prices
Tech Supply Direct - Premium Refurbished Servers & Workstations at Unbeatable Prices
Digital Ocean Offer Code
![]() DigitalOcean: AI-Powered Unified Inference Cloud Infrastructure
DigitalOcean: AI-Powered Unified Inference Cloud Infrastructure
HostiFi UniFi Cloud Hosting Service
![]() HostiFi - Fast and Reliable UniFi in the Cloud
HostiFi - Fast and Reliable UniFi in the Cloud
Protect your privacy with a VPN from Private Internet Access
![]() https://www.privateinternetaccess.com/pages/buy-vpn/LRNSYS
https://www.privateinternetaccess.com/pages/buy-vpn/LRNSYS
Patreon
![]() https://www.patreon.com/lawrencesystems
https://www.patreon.com/lawrencesystems
Chapters
00:00 pfsense WIreguard site to site VPN tutorial
01:00 Demo Setup and How Wireguard Tunnels Work
03:44 Wireguard Peers and Keys
04:57 How To Configure Wireguard Tunnels and Peers
07:32 Assigning Wireguard Tunnels to pfsense interfaces
10:00 Configuring Static Routes in pfsense for Wireguard
11:43 Firewall Rules and Testing Wireguard VPN
14:52 Wireguard VPN and NAT
18:00 Production Wireguard VPN and Common Mistakes