I followed Tom’s tutorial and have set up pfblockerNG, it works fantastic. Then I noticed something that made me a bit worried:
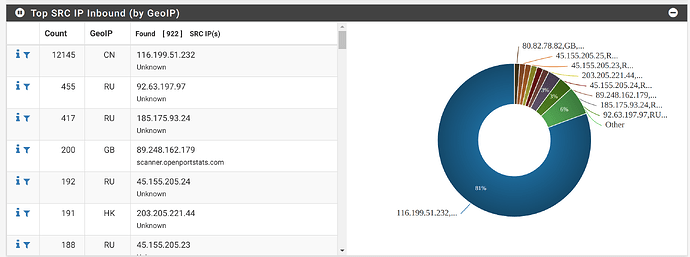
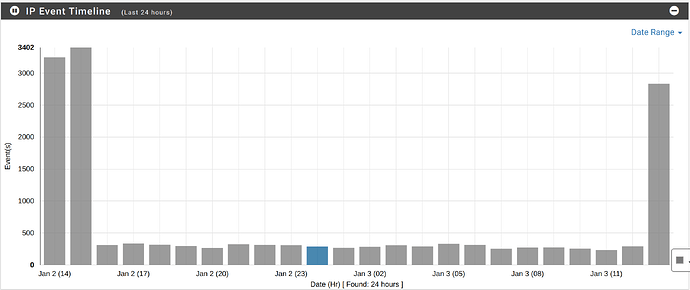
Once I have GeoIP turned on and enabled the top spammer list (ipv4), deny inbound, then I started to see pfsense reporting a huge amount of inbound denies from a Chinese IP, which is poking only port 6690, and it’s trying different outbound ports to reach me.
The 6690 port is the default of Synology Drive and it was open. After seeing these huge amount of attempts I closed port 6690 on my pfsense, also turned off the synology.me DDNS, set up alias in Synology which makes Drive go through other port.
Surprisingly, the amount of attempts from that Chinese IP dropoed significantly after I took action, it went less active for a few hours but now it goes full throttle again.
I had a few ports open at that moment: HTTPS, SMTP, SMTP-TLS, IMAP/S, 5006, 6690, and a custom DSM HTTPS port. Now 6690 is closed.
The huge amount of attempts shocked me quite a bit. There are many ports of Synology that could be open, only targeting 6690 seems a bit weird to me too.
Is this kind of things normal or am I really seeing a targeted attempt?
Once some automated system learn you have a port open, or they find it via a service such as Shodan.io, they automatically start running through what ever popular vulnerabilities they have configured in an attempt to get in. Don’t take it personally.
1 Like
That’s good to know. Thank you Tom!
I guess the only thing I should do now is to set up my Synology as good as possible.
QNAP and Synology NAS’s are constantly having issues with security, stick 2FA on your box ! That seems to thwart many past issues.
Open ports, can’t see too many reason to! Use OpenVPN to access your network it’s pretty robust.
1 Like
I would really love to use OpenVPN but I couldn’t. My work laptop has its own Cisco VPN running and connected to the company network already.
2FA looks like a good idea, I’ll take a look into it.
What I have learned so far is that changing ports to a random number will reduce the risk significantly. Some companies run their Synology server exposed to the internet, there must be a way to make it secure enough.
Too bad Windows Syno Drive Client refuses to use any port other than 6690, while iOS Drive app is happy to use the HTTPS port, with the alias and custom domain that I have set up. Quite some small bugs or quirks here and there as far as I can see.
1 Like