I’ve configured pfSense per the tutorial and I’m seeing my defined clients routing through PIA as desired. This is fantastic. However, I discovered a gotcha. Those clients lose access to other VLANs. I modified the rule that sends traffic to PIA to include destination NOT RFC1918 thinking that would make the traffic no longer match that rule if I was trying to get to any local subnet but that didn’t appear to work.
What is the most effective and secure way to exclude local traffic from this rule?
Thanks!
You could create a rule on LAN above the ones that do the VPN gateways and matches the desired destination on LAN2 (or just LAN2 Net) and uses * as the gateway.
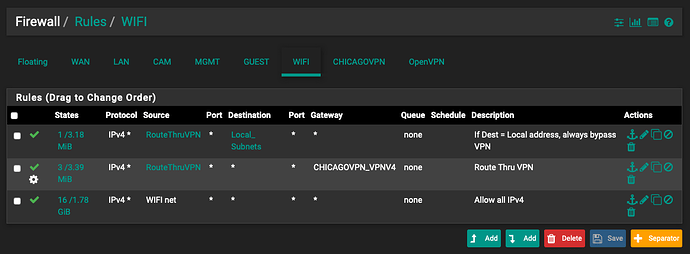
Thanks Tom. Things are not behaving right at all now. Here are my rules.
As soon as I enable the VPN client all of my devices are being routed through VPN, in spite of that rule being there. Even if I disable the two top rules, all WiFi devices continue to have a VPN IP address. I’m missing something simple here. I had this working yesterday and backed it all out because I couldn’t figure out a way to create an exception. I’m still not sure my exception rule will work but right now I can’t even stop everyone from going through the VPN.
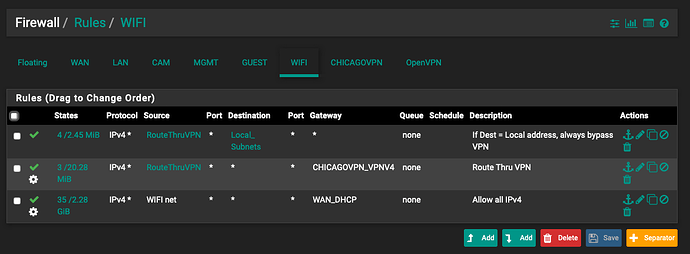
I’ve banging on this all day to no effect. I’ve made some progress. I have the exception working. However the only way to force traffic off of the VPN is to specify the WAN_DHCP gateway on the last rule.
So now devices included in the alias go out the VPN for all Internet traffic but can still access local resources. However, with that WAN_DHCP gateway declared on the last rule I can no longer reach the other VLANs from other devices on the WIFI VLAN. I’m perplexed.
I found the problem. I needed to leave the gateway at default for the last rule. I also needed to check the “Don’t Pull Routes” option in the VPN Client settings. Now everything works as expected. Without that box checked, everything was getting routed through the VPN regardless of the rules.
2 Likes