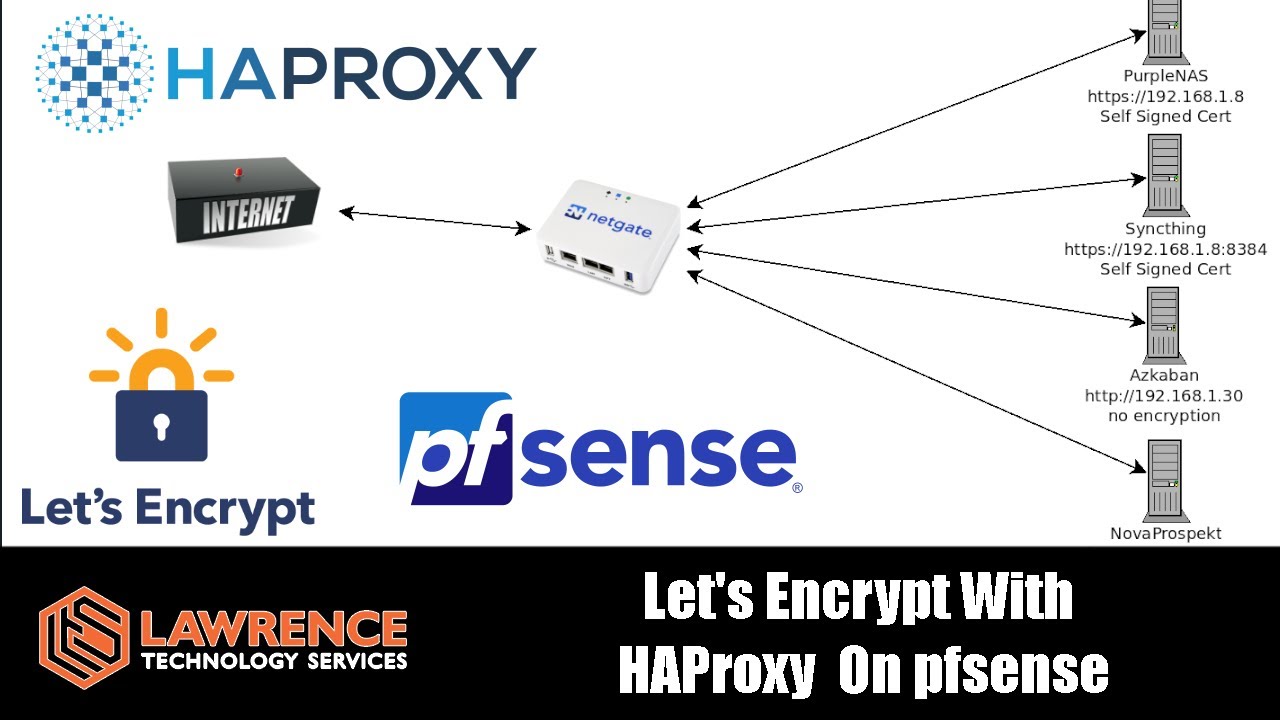
I have seen several helpful posts from this forum but I would like to request a guide or video for setting up a plex server with FQDN (plex.somedomain.com) with the above mentioned combo:
Cloudflare to handle proxied DNS of plex.somedomain.com
PFsense as the primary router to handle encryption offloading
HAProxy to handle the reverse proxy of the subdomain
Plex to act as the server (Ideally in an unraid docker or something similar)
I have setup the combo before but I would like to make sure I am doing it in the most efficient and secure manner.
I cover that in this video.
The only difference is that I used Digital Ocean for the domain DNS and the port would be different than the example for Plex in the HA Proxy server settings.
Tom, this was a great video and help me understand the pfsense. I have it all set but i’m getting a 503 error inside or outside of my home when i hit my plex.domain.tld
Using the same frontend I’ve been able to setup another internal server just fine. Just the Plex server giving the 503
Any insight you can throw my way would be much appreciated.
EDIT: Found out the issue was with the frontend. I split the frontend into individual shared sites and everything started working.
Using this setup and it is working great.
Question:
Recently I have determined that my internal plex players are using DNS → Cloudfare → back to my router → back to my server.
This seems very inefficient for local LAN traffic. How can we ensure that DNS routing for plex utilizing this setup can be routed directly to the plex server? I don’t see any configuration that would route local traffic directly to the defined servers.
Thanks in advance.
For others searching, I am in the process of attempting to follow this tidbit to accomplish the LAN redirection:
1 - You’ll have to set up a second front-end in HAProxy to listen on your LAN. Assuming you have one set up to listen on your WAN just copy it entirely, but change the interface it’s listening on to your LAN gateway. It should already be using the LetsEncrypt cert you generated for the WAN front-end.
(As a side note you can define a VIP and use it instead of your LAN gateway, or multiple VIPs and multiple front-ends in HAProxy to pair together. This can be useful because it allows you to define access rules based around the IP addresses you assign the VIPs if you need/want to segment access to sites inside your LAN)
2 - You’ll Need to setup Hostname Overrides in DNS Resolver for each site. Have each override record point at the IP address of the interface that HAProxy is listening to on your LAN. This will force DNS requests on your internal network for the sites you’re hosting to point back to the HAProxy front-end on your LAN.