Hi all
I want to block a host from talking to other hosts in the same subnet/interface.
I’ve got an alias of server1 1.2.3.4 and another alias of server2 1.2.3.5. I want to block Comms between server 1 & 2, so on the interface that both hosts reside on I’ve put a block rule:
Block
Source Single Host/Alias: server1
Any protocol
Destinations: Alias for server2
However, they can still talk.
So I’m not sure what I need to do to get them to stop talking, the block rule is enabled on the interface where both IPs live.
PS: I checked states between 1&2 and none existed.
Any help greatly appreciated
Thanks.
The problem is that the traffic will be handled in the switch and never make it to the firewall. You would need to figure out how to block those communications on the host firewalls.
1 Like
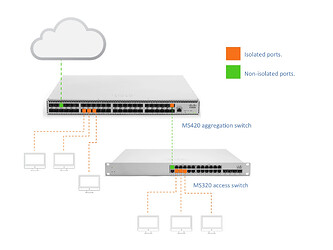
@Chris_sctech If your switch supports port isolation (a.k.a. Private VLAN) . You are in luck. Else you are out of luck.
port isolation is the function if a L2 switch to prevent hosts connected on isolated ports to be able to communicate with each other. Even if the hosts are on the same L2 network domain.
- isolated port to isolated port = no go.

- isolated port to non-isolated port = Works.

Q: What kind of switch do you have sitting in between your hosts and your pfSense Firewall ?
Actually, the two hosts are VMs within XCP-NG, which goes direct to pFsense.
Yep your probably correct there … it’ll all be in the virtual switch within XCP-NG and as you say will never actually make it to pFsense…
Ok so I need to look at the firewalls directly on the VMs themselves.
Thanks.