I am wanting to change the way I use/allocate IP addresses on my network as well as how I am using VLANs. Currently, I only use a few VLANs (Family, Guest, Printers) and I also have a remote network via OpenVPN. My IP addresses are based around 10.3.x.x with the third octet being the network (16 = LAN, 17 = Remote, 18 = Family, 19 = Guest, 20 = Printer) and the last octet is broken into arbitrary ranges that I use to help identify the device, such as all addresses in the 50 range are storage servers and all the addresses in the 30 range are IP cameras.
What I want to move to is something like: 10.{Site/Floor}.{VLAN}.{Device} for for example all the Wifi APs in the basement would be 10.10.20.x and all the Wifi WPs on the main floor would be 10.11.20.x I am thinking of making the following VLANs: Management, Printers, Cameras, Servers, Storage, Guest, Family, Kids, IP Phones, IPMI, etc.
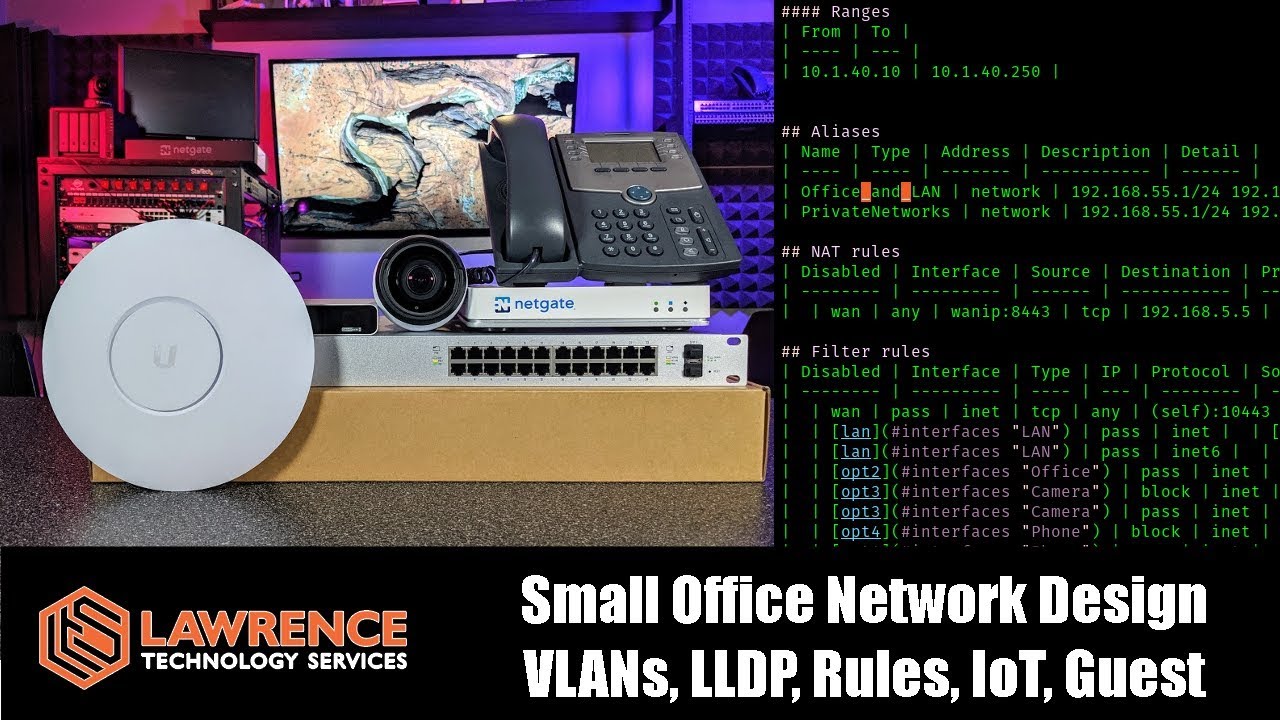
I am however not sure if I will end up with a mess in pfSense where I have a bunch of routing between networks as the servers and the storage need to communicate and would using a subnet of 255.0.0.0 vs 255.255.255.0 make a difference? Ideally, i would only have to inter-route the various VLANs as required but each floor could talk to the devices on another floor without issue.
If you want to separate all the networks like that so your network is not flat, you will have to write a lot of rules for all the things to talk to each other.
1 Like
I was thinking that if i flip the second and third octet that it would make for fewer rules needing to be created and simplify the setup, so it would be 10.{VLAN}.{Site/Floor}.{Device}
That way all the APs would be on the same VLAN / network if the correct subnet is used.
1 Like
It isn’t clear to me what advantage there is to having separate vlans based on the floor.
Are you going to have different SSIDs on each floor?
Do you want your mobile to get a different ip address when you walk upstairs?
To me it would make more sense to the the last octet to encode floor, if you want to have the physical location “encoded” into the ip address. Then use reservations for your fixed location wired devices. And may use a range for your roaming wireless devices.
Ideally, i would only have to inter-route the various VLANs as required but each floor could talk to the devices on another floor without issue.
If that’s the case, then have the same vlan for the type of device, e.g. guest, IoT, etc. It shouldn’t matter which AP the guest is connecting through, you want the access restrictions to be based on the SSID they connected to, and there should be a one-to-one between SSID and vlan; at least that is the way I would set it up.
Separating by floor is not a requirement, though I am wanting to sorta develop as system I can use for a small all they way to large network. I am using my home-lab as a test bench so to speak for working on my networking skills. The SSIDs would be the same no matter what floor you are on.
For example I run 6 different managed switches, 4 are in the basement, 1 on the main floor and 1 upstairs. I also have 3 APs with 2 on the main floor and 1 upstairs. So with my new design they would go something like this: 10 = management, 20 = Wireless AP, 30 = servers
Switch 1 = 10.10.10.1
Switch 2 = 10.10.10.2
Switch 3 = 10.10.10.3
Switch 4 = 10.10.10.4
Switch 5 = 10.10.11.1
Switch 6 = 10.10.12.1
AP1 = 10.20.11.1
AP2 = 10.20.11.2
AP3 = 10.20.12.1
I would want all the switches to be reachable between each other and also from my laptop using the management VLAN and the APs would talk to the unifi controller that would say be at 10.30.10.1
When I look at your vlans I’d say you’ll have some duplication so basically identical rules for two vlans.
What I’ve noticed on my network, the netgear switches and TP-link AP like to have a management vlan defined, hence it’s probably a good idea to put all your networking infrastructure on the same management vlan.
The best approach is to see what works for you, but I would start off simple so I get the rules sussed out. Then I would see what the steps are to add an extra vlan.
As a comparison I have a Management / ISP / VPN / CAM / IoT / Guest vlan set up, I lock down the Cam / Guest / Iot vlans.