I seem to experiencing some DHCP “leakage” between VLANs.
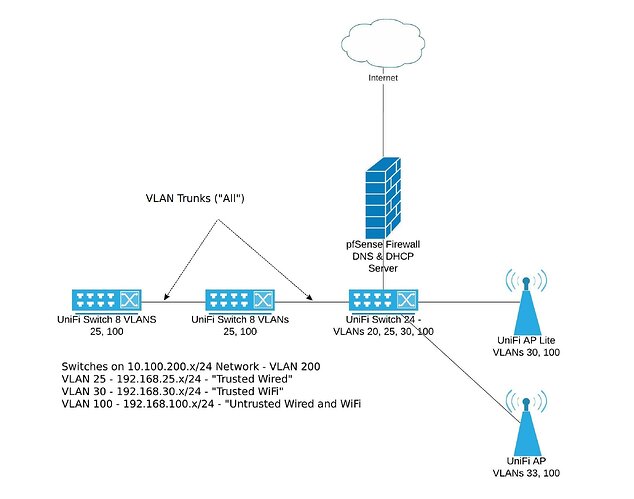
I have my switches on the 10.100.200.x/24 network (VLAN 200).
There are three “user” VLANs:
- VLAN 25 - Trusted wired devices using the 192.168.25.0/24 network
- VLAN 30 - Trusted WiFi devies using the 192.168.30.0/24 network
- VLAN 100 - Untrusted wired and WiFi devices on the 192.168.100.0/24 network
There is one server VLAN - VLAN 20 using the 192.168.20.0/24 network (not in the diagram below).
pfSense (2.4.5) is providing DHCP and DNS services.
The switches are a UniFi Switch 24 and 2 UniFi Switch 8s. The switches are using firmware 4.0.80.10875.
Trunks between the switches and the pfSense box are configured to “ALL” VLANs.
The user ports on the UniFi Switch 8 are tagged for VLAN 100 (Untrusted) for IoT devices or VLAN 25 for trusted wired devices (except for the uplink/downlink ports).
The problem is that when an IoT device (e.g. Roku, LG smart TV) on the switch in the TV room requests a DHCP address, it is receiving a VLAN 20 address from the 192.168.20.0/24 network (used by the servers) instead of a 192.168.100.0/24 network. It seems that a trusted device (e.g., a laptop) is plugged into a port tagged with VLAN 25 it receives an address on the 192.168.25.0/24 network as expected.
I have verified that switch port VLAN assignments are correct. The DHCP servers on the pfSense box has DHCP running for each of the subnets and there are available IPs for lease. Even statically assigning an IP (in the 192.168.100.0/24 subnet) to a device does not work - it still gets a 192.168.20.0/24 address.
I also rebooted the switches and pfSense firewall to “clear out” any lingering DHCP reservations without luck. (Yes, the IoT devices are using DHCP ![]() ).
).
Any ideas what is going on here?
Thanks